Ranter
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Comments
-
 Kimmax106837yWell, the idea isn't as stupid as it might sound, think of the CCleaner binaries that somehow got malware included on their way to the website.
Kimmax106837yWell, the idea isn't as stupid as it might sound, think of the CCleaner binaries that somehow got malware included on their way to the website.
However, I don't think AV scanning the binary is going to detect any malicious modifications in the code base itself, since scanning for known malicious binaries/hashes is still, sadly, the way most AV matches are being made. I don't think heuristics would catch these.
Somehow chaining the binaries after the build on their way to distribution might be a bigger attack vector tho, so providing a way to, for example, compare the file hashes in the backend with the ones from the build system might be an option -
 gc944447y@Kimmax We have a continuous integration / delivery pipeline where every code change needs reviews, builds passing and automatically tested and deployed.
gc944447y@Kimmax We have a continuous integration / delivery pipeline where every code change needs reviews, builds passing and automatically tested and deployed.
I have asked them to audit the Deployment process as there is no manual step except for coding and they still go on and on about this AV scan. -
 gc944447y@S-Homles-MD So you do a Malware scan?
gc944447y@S-Homles-MD So you do a Malware scan?
How often? Every check in?
If it can be magically automated somehow, I don't mind doing that scan and getting this whole thing done and over with.
Related Rants

 Did you say security?
Did you say security?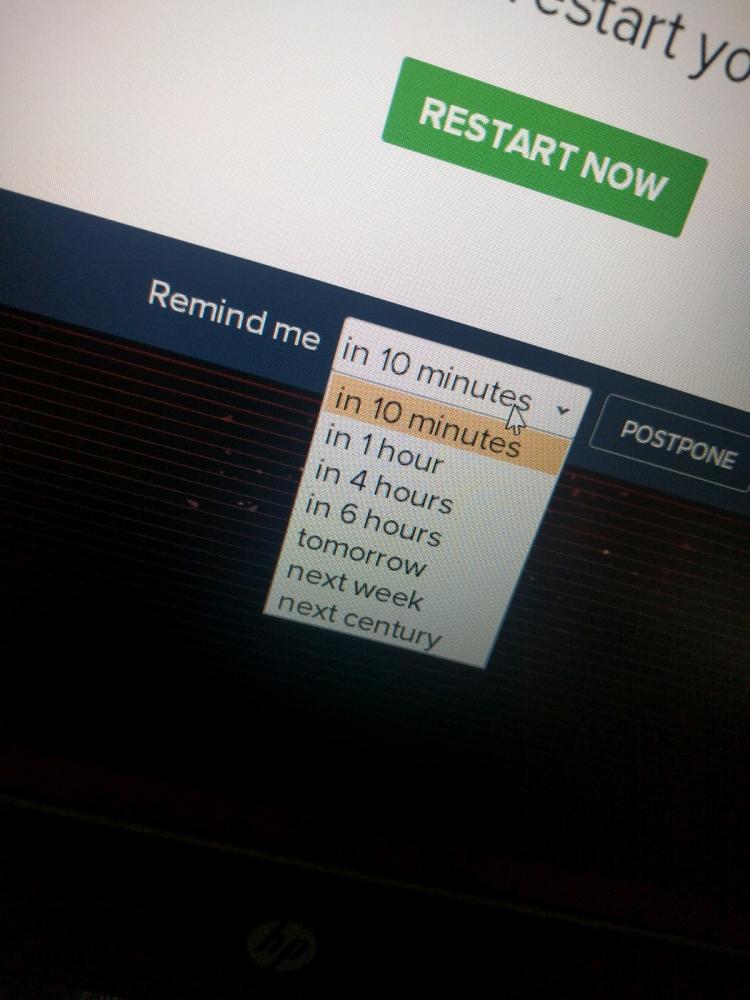 10 points for next century option.
10 points for next century option.
How did you get the people from Info Security and Compliance on board this continuous delivery thing ?
I am being asked to run antivirus scans on my own code and binaries as part of build.
Is this common practice? Am I missing something?
I am going to deploy stuff on Azure PaaS. I can understand having malware scan agent on azure VMs scanning the infra, but this?
question
cloud
security
confused
devopslife