Ranter
Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Comments
-
@Lor-inc Not yet as it's very much a work in progress and if someone would use it as 'secure', that would be a problem 😅
But, to give you an image of what the framework does;
Everything works based on a router which routes based on a config file to decrease the risk of file inclusion vulns. The router (all based on the config file) automatically performs rate limiting if configured for the specified route and checks if the parameters (put/post/whatever) are according to the configured requirements. The router also checks if authentication is required and if yes, does automated checks and so on. It's actually very tiny! -
taiga05yI am also working in a team which provide RESTful API services, we keep finding the history issues due to the bad design before, I would say it it something very hard to avoid as the product evolve.
Recently thinking about a new side project to build some framework to handle the security check issue, but one thing is, we cannot mess the existing integration so the framework must has some whitelist and it is not able to be perfect -
@taiga
It's only hard to avoid if your company is willing to neglect rigor and discipline.
If your testing suite doesn't test endpoint security and validation, or have basic fuzzing, and you don't whitebox test, you're shipping unfinished work. I don't know of any legitimate companies that also don't pay for external audits and blackbox testing. It's something that almost all insurance requirements will demand. -
taiga05y@SortOfTested
I would not say my company (at least as a rookie dev as me) is "willing" to neglect rigor and discipline.
maybe I did not give enough context, basically my team is API team which focus on the business logic implementation via our code, there is a separate team handling the security check work, however, things got lost and messed up during many times of product ownership transfer / reorg, our team are expected to provide some extra security check for specific endpoints besides the existing check (due to some fresh new hacker tech), it is kind of breaking change for the users who already integrated with us.
it is just a example how we should design the system well so we don't have those historical debt, the designer of the architecture was good at that time, but he was not able to know how the industry or technology changes, what new requirements comes, that is what I mean by "hard". -
 Hazarth91945yDo you have a blog, youtube channel, livestream or something where you share this knowledge? I'd love to learn from the experiences of someone who does 3hrs of security checks for something small and fun
Hazarth91945yDo you have a blog, youtube channel, livestream or something where you share this knowledge? I'd love to learn from the experiences of someone who does 3hrs of security checks for something small and fun -
@Hazarth I do have a blog which i haven't updated since 2018 (just noticed the ssl cert is fucked) but i plan on posting again on there soon!
I don't use any social media or any blogging platforms, except for my own.
Related Rants

 Did you say security?
Did you say security?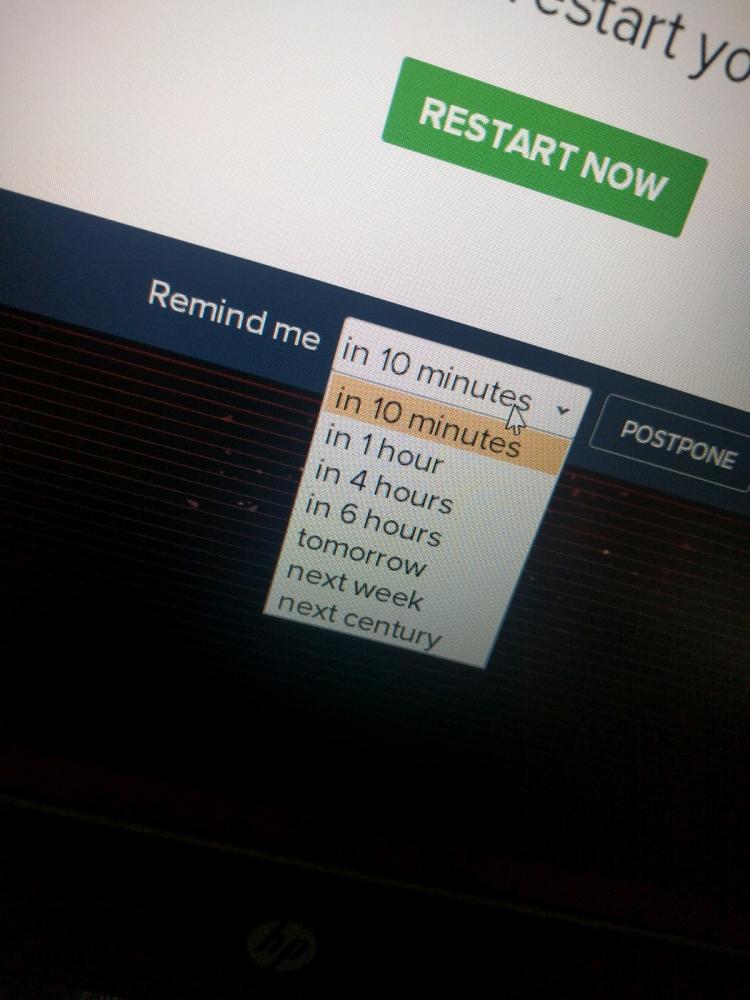 10 points for next century option.
10 points for next century option.
I think I ranted about this before but fuck it.
The love/hate relation I have with security in programming is funny. I am working as a cyber security engineer currently but I do loads of programming as well. Security is the most important factor for me while programming and I'd rather ship an application with less features than with more possibly vulnerable features.
But, sometimes I find it rather annoying when I want to write a new application (a web application where 90 percent of the application is the REST API), writing security checks takes up most of the time.
I'm working on a new (quick/fun) application right now and I've been at this for.... 3 hours I think and the first very simple functionality has finally been built, which took like 10 minutes. The rest of the 3 hours has been securing the application! And yes, I'm using a framework (my own) which has already loads of security features built-in but I need more and more specific security with this API.
Well, let's continue with securing this fucker!
rant
security
cyber security