Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "cyber security"
-
buzzword translations:
"cloud" -> someones computer
"big data" -> lots of somewhat irrelevant data
"ai" -> if if if if if if if if if if if if if else
"algorithm" -> something that works but you don't know why
"secure" -> https://
"cyber security" -> kali linux + black hoodie
"innovation" -> adding something completely irrelevant such as making a poop emoji talk
"blockchain" -> we make lots of backups
"privacy" -> we store your data, we just don't tell you about it40 -
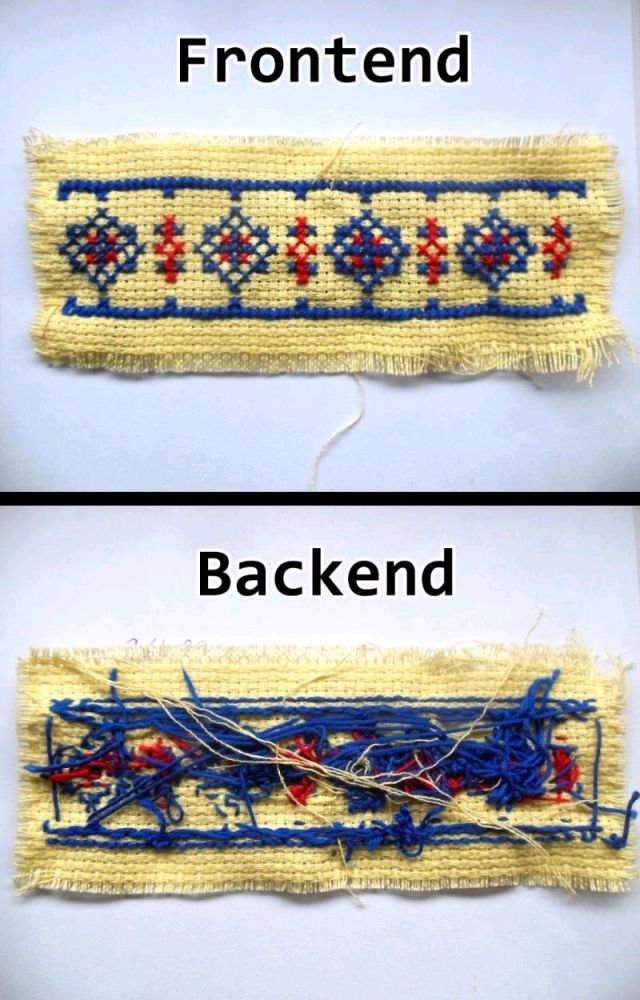
Our designer (and frontender) just saved my ass big time. Had to do a tiny project involving design and frontend so I gave it a try and it looked like crap, deadline in a week. The designer made the most beautiful thing in like two days.
Kudos to all designers for doing what they're good at and ensuring that we, backenders (and cyber security people for that matter), can do our thing without having to worry about knowing how to design stuff and create interfaces because we might hate doing that and sometimes just really suck at it.
Kudos designer guys/girls!8 -
A while ago (few months) I was on the train back home when I ran into an old classmate. I know that he's a designer/frontend/wordpress guy and I know that he'll bring anyone down in order to feel good. I also know that he knows jack shit about security/backend.
The convo went like this:
Me: gotta say though, wordpress and its security...
Him: yeah ikr it's bad. (me thinking 'dude you hardly know what the word cyber security means)
Me: yeah, I work at a hosting company now, most sites that get hacked are the wordpress ones.
Him: yeah man, same at my company. I made a security thing for wordpress though so we can't get hacked anymore.
Me; *he doesn't know any backend NOR security..... Let's ask him difficult stuff*
Oh! What language did you use?
Him: yeah it works great, we don't get hacked sites anymore now!
Me: ah yeah but what language did you use?
Him: oh it's not about what language you use, it's about whether it works or not! My system works great!
Me: *yeah.....right.* oh yeah but I'd like to know so I can learn something. What techniques did you use?
Him: well obviously firewalls and shit. It's not about what techniques/technology you use, it's about whether it works or not!
That's the moment I was done with it and steered the convo another way.
You don't know shit about backend or security, cocksucker.16 -
You think a junior dev pushing his code onto a production server is bad? Wait till you have that admin who is illegally mining Bitcoin on your production server. 😂
I went for a Cyber Security conference today with one of managers and this was one of the life experiences some of the speakers shared.19 -
So I've been looking for a Linux sysadmin job for a while now. I get a lot of rejections daily and I don't mind that because they can give me feedback as for what I am doing wrong. But do you know what really FUCKING grinds my FUCKING gears?
BEING REJECTED BASED ON LEVEL OF EDUCATION/NOT HAVING CERTIFICATIONS FOR CERTAIN STUFF. Yes, I get that you can't blindly hire anyone and that you have to filter people out but at least LOOK AT THEIR FUCKING SKILLSET.
I did MBO level (the highest sub level though) as study which is considered to be the lowest education level in my country. lowest education level meaning that it's mostly focused on learning through doing things rather than just learning theory.
Why the actual FUCK is that, for some fucking reason, supposed to be a 'lower level' than HBO or Uni? (low to high in my country: MBO, HBO, Uni). Just because I learn better by doing shit instead of solely focusing on the theory and not doing much else does NOT FUCKING MEAN THAT I AM DUMBER OR LESS EDUCATED ON A SUBJECT.
So in the last couple of months, I've literally had rejections with reasons like
- 'Sorry but we require HBO level as people with this level can analyze stuff better in general which is required for this job.'. - Well then go fuck yourself. Just because I have a lower level of education doesn't FUCKING mean that I can't analyze shit at a 'lower level' than people who've done HBO.
- 'You don't seem to have a certificate for linux server management so it's a no go, sorry!' - Kindly go FUCK yourself. Give me a couple of barebones Debian servers and let me install a whole setup including load balancers, proxies if fucking neccesary, firewalls, web servers, FUCKING Samba servers, YOU FUCKING NAME IT. YES, I CAN DO THAT BUT SOLELY BECAUSE I DON'T HAVE THAT FUCKING CERTIFICATE APPEARANTLY MEANS THAT I AM TOO INCOMPETENT TO DO THAT?! Yes. I get that you have to filter shit but GUESS WHAT. IT'S RIGHT THERE IN MY FUCKING RESUME.
- 'Sorry but due to this role being related to cyber security, we can't hire anyone lower than HBO.' - OH SO YOUR LEVEL OF EDUCATION DEFINES HOW GOOD YOU ARE/CAN BE AT CYBER SECURITY RELATED STUFF? ARE YOU MOTHERFUCKING RETARDED? I HAVE BEEN DOING SHIT RELATED TO CYBER SECURITY SINCE I WAS 14-15 FUCKiNG YEARS OLD. I AM FAMILIAR WITH LOADS OF TOOLS/HACKING TECHNIQUES/PENTESTING/DEFENSIVE/OFFENSIVE SECURITY AND SO ON AND YOU ARE TELLING ME THAT I NEED A HIGHER LEVEL OF FUCKING EDUCATION?!?!? GO FUCKING FUCK YOURSELF.
And I can go on like this for a while. I wish some companies I come across would actually look at skills instead of (only) study levels and certifications. Those other companies can go FUCK THEMSELVES.39 -
Currently at a cyber security event.
The most ironic thing is that the WiFi here is not secured...20 -
I'm a week into my new job right now. What do I love the most about it?
Learning things all day long and getting paid for it!
I'm learning about hosting things, DNS, cyber security, configurations, Linux (although my current skill set with Linux has been enough for now) and so on!
Hell, easy day today (not that many tickets) so decided to start learning Ansible! Next to that I've gotta learn vim (it just autocorrected that to cum.... O.o), work with hosting panels, mail stuffs (dns, debugging etc etc) and so fucking on.
The boss hasn't been at location yet which will happen tomorrow but he seemed like a very chill guy.
I love this!21 -
I'm a programmer and an aspiring cyber security specialist. Yesterday, after I gave a presentation about smart bulb hacking, I heard through a coworker that a cyber security company is interested in talking to me. Yay!11
-
Got a call from a recruiter today. (Keep in mind that using WhatsApp is about a requirement over here.)
R: so can I app you (I hate that word to the fucking point) with further details?
Me: *oh fuck this is gonna get me fucked again* uhm I don't use it so yah...
R: ohhh okay, security reasons?
Me: *slight relief* yes indeed, sir
R: oh fair enough, you can always just text and call me!
*very relieved feeling*
It's for either a cyber security or linux job by the way.28 -
Cybersecurity:
>nothing happens
>I can't believe we pay your useless ass to sit around doing nothing all day!
>something happens
>this is your fault1 -
(The PM is pretty technical)
One day:
Me: Could you create this subdomain?
PM: Sure, just a sec.
Me: Ohh and could you add a letsencrypt cert? (one click thingy)
PM: Why would you need that on this kinda site...
Me: Well in general for security...
PM: Nahh.
*walks away*
Next day:
(referring to my internship manager/guider as Bob)
Bob: Hey... we have a new subdomain!
Me: Yup!
Bob: Wait why is there no letsencrypt certificate installed...?!?
Me: Well, the PM didn't find that neccesary...
Bob: (Oo) of course it is... are we going for security by default or what?
Me: Yup agreed.
Bob: *creates cert and sets everything up in under a minute*
It wasn't a high profile site (tiny side project) but why not add SSL when you can for free?8 -
Me: So what you are doing in the IT field?
Him: I am hacking bank websites.
Me: OK, that's cool. It is good in free time. What is your actual job?
Him: I am seriously hacking the bank Web site!
Me: Trust me, if you seriously doing that you will never ever mentioned it...
Him: No, I am doing it legally... The bank hiring me to try to hack the website...
Me: OK, you mean that you are cyber security tester?
Him: That is almost the same...
Me: So you are tester?
Him: I am hacking bank's websites...
Me:....7 -
Someone asked for an RSS feed for the security/privacy blog, I thought?
Well, hereby! There are three feeds:
https://much-security.nl/main.xml - a feed which is updated with both blog posts and external links relating to privacy/security I find interesting/useful.
https://much-security.nl/own.xml - a feed only containing the blogs posts themselves. For people who are only interested in that part.
https://much-security.nl/external.x... - a feed only containing external links. For people who'd like to stay updated on recent cyber security/privacy thingies.
Tracking: every time a feed is visited, a redis value for that feed get's incremented. No time, ip addresses, user agent or whatsoever is saved. Just one variable getting increased once.
New domain name will also be revealed soon (probs tomorrow, going to bed soon as I've just been sick) :D.
Oh and just a warning, the main/external feed are the only ones populated with exactly one item right now :P30 -
A: There is not even a single forum for cyber security. Let's build one.
Me: Are you sure that there is not even a single forum?
A: Yes, I'm a cyber security expert. I have 5 years of experience in this field.
Me: **walks out quitely**1 -
Fucking China!
The only time they ever come out of their pathetic walled internet is to attack your servers.
Fuck that country.10 -
Paranoid Developers - It's a long one
Backstory: I was a freelance web developer when I managed to land a place on a cyber security program with who I consider to be the world leaders in the field (details deliberately withheld; who's paranoid now?). Other than the basic security practices of web dev, my experience with Cyber was limited to the OU introduction course, so I was wholly unprepared for the level of, occasionally hysterical, paranoia that my fellow cohort seemed to perpetually live in. The following is a collection of stories from several of these people, because if I only wrote about one they would accuse me of providing too much data allowing an attacker to aggregate and steal their identity. They do use devrant so if you're reading this, know that I love you and that something is wrong with you.
That time when...
He wrote a social media network with end-to-end encryption before it was cool.
He wrote custom 64kb encryption for his academic HDD.
He removed the 3 HDD from his desktop and stored them in a safe, whenever he left the house.
He set up a pfsense virtualbox with a firewall policy to block the port the student monitoring software used (effectively rendering it useless and definitely in breach of the IT policy).
He used only hashes of passwords as passwords (which isn't actually good).
He kept a drill on the desk ready to destroy his HDD at a moments notice.
He started developing a device to drill through his HDD when he pushed a button. May or may not have finished it.
He set up a new email account for each individual online service.
He hosted a website from his own home server so he didn't have to host the files elsewhere (which is just awful for home network security).
He unplugged the home router and began scanning his devices and manually searching through the process list when his music stopped playing on the laptop several times (turns out he had a wobbly spacebar and the shaking washing machine provided enough jittering for a button press).
He brought his own privacy screen to work (remember, this is a security place, with like background checks and all sorts).
He gave his C programming coursework (a simple messaging program) 2048 bit encryption, which was not required.
He wrote a custom encryption for his other C programming coursework as well as writing out the enigma encryption because there was no library, again not required.
He bought a burner phone to visit the capital city.
He bought a burner phone whenever he left his hometown come to think of it.
He bought a smartphone online, wiped it and installed new firmware (it was Chinese; I'm not saying anything about the Chinese, you're the one thinking it).
He bought a smartphone and installed Kali Linux NetHunter so he could test WiFi networks he connected to before using them on his personal device.
(You might be noticing it's all he's. Maybe it is, maybe it isn't).
He ate a sim card.
He brought a balaclava to pentesting training (it was pretty meme).
He printed out his source code as a manual read-only method.
He made a rule on his academic email to block incoming mail from the academic body (to be fair this is a good spam policy).
He withdraws money from a different cashpoint everytime to avoid patterns in his behaviour (the irony).
He reported someone for hacking the centre's network when they built their own website for practice using XAMMP.
I'm going to stop there. I could tell you so many more stories about these guys, some about them being paranoid and some about the stupid antics Cyber Security and Information Assurance students get up to. Well done for making it this far. Hope you enjoyed it. 26
26 -
Anyone here who also got super bored while on a porn site and ended up pentesting that porn site..?14
-
Got called up today by my org's cyber security team.
Reason: Installed a font called "Hack" (https://github.com/source-foundry/...)
🤦♂️🤦♂️🤦♂️🤦♂️🤦♂️1 -
I watched the news recently and they talked about cyber security.
To demonstrate "how serious the topic is" they showed a screen with a terminal and literally pinged google.com.
I thought that was funny7 -
I think I ranted about this before but fuck it.
The love/hate relation I have with security in programming is funny. I am working as a cyber security engineer currently but I do loads of programming as well. Security is the most important factor for me while programming and I'd rather ship an application with less features than with more possibly vulnerable features.
But, sometimes I find it rather annoying when I want to write a new application (a web application where 90 percent of the application is the REST API), writing security checks takes up most of the time.
I'm working on a new (quick/fun) application right now and I've been at this for.... 3 hours I think and the first very simple functionality has finally been built, which took like 10 minutes. The rest of the 3 hours has been securing the application! And yes, I'm using a framework (my own) which has already loads of security features built-in but I need more and more specific security with this API.
Well, let's continue with securing this fucker!10 -
I'm soon graduating from a tech/IT school which recently specialized in cybersecurity.
Today when I changed my password on their website, it displayed the old one in clear text.
God damn it people, THIS is the reason why our school's reputation has been slowly but steadily going down. 1
1 -
Some years ago I was in cyber security in the military being shown some new tech for our use. Was challenged to try and get past it after being explained it's basics. Took me one long line in Linux about 10 seconds.
Anomaly detection firewall with machine learning seemed like a good idea.
Setting it to aggressive response and then change the package header to the firewall's own address however made it kill itself.
We didn't deploy that firewall that I know of.5 -
Who's at fault for the recent Wanna Cry virus: The companies affected or Microsoft/NSA?
Personally, I think it's the companies affected. This is what happens when you try and be cheap when it comes to cyber security.8 -
Cyber security. Deep knowledge of cyber security and networks is what I wish I had. The math stuff that no one bothers with, specifically.6
-
!rant 📚 📑
Cybersecurity books @Humble Bundle
https://humblebundle.com/books/...
There is a really great Humble Book Bundle at the moment, starting at 1$. The bundle contains several cyber security books ("Practical Reverse Engineering" and "Security Engineering" have a good reputation).8 -
This isn’t gonna be a random because I do eventually get to a Tech and YouTube related topic.
YouTube is actually killing itself with all of the dumbass rules they’re implementing. Trying to child proof or limit educational content is genuinely a shit policy. The reason so many gaming channels are switching to twitch because it doesn’t try to censor you.
But now I don’t know if you’ve heard but YouTube updated their guidelines and they’re no longer allowing content that teaches people about Hacking essentially (and I hate putting it like that but I can’t remember the exact words they used Hacking just summarizes it) which is fucking ridiculous like what the fuck else, are they gonna stop allowing lock picking videos?
YouTube has always been an amazing FREE resource for people learning Programming, Cyber Security, IT related fields, and even shit like lock picking, cooking, car stuff, and all that stuff. Even sometimes when the tutorials aren’t as detailed or helpful to me they might be exactly what someone else needed. And Cyber Security can be a difficult topic to learn for free. It’s not impossible far from it, but YouTube being there was always great. And to think that a lot of those could be taken down and all of the Security based channels could either lose all revenue or just be terminated is terrifying for everyone but more so them.
A lot of people and schools rely on YouTube for education and to learn from. It’s not like YouTube is the only resource and I understand they don’t want to be liable for teaching people that use these skills for malicious purposes but script kiddies and malicious people can easily get the same knowledge. Or pay someone to give them what they want. But that’s unfair to the people that don’t use the information maliciously.
It’s the same for the channels of different topics can’t even swear and it’s ridiculous there’s so many better options than just banning it. Like FUCK kids nowadays hear swearing from their older siblings, parents, friends, and TV it’s inevitable whether someone swears or not and YouTube is not our parents, they aren’t CBS, so stop child proofing the fucking site and let us learn. Fuck.
TLDR YouTube is banning educational hacking videos and are being retarded with rules in general16 -
Fucked!
I have got my cyber security exam tomorrow morning and i just got a call from a client to make some urgent changes to his site.
To add to it, i already wasted around half an hour becoz GoDaddy Plex somehow decided to block my own IP in the firewall.
And now I am on devRant.
Crap. I am fucked!4 -
I am tired of my idiot ‘friends’ asking me if I can hack Facebook Instagram etc. because some other idiot made them mad. Like fuck no. 1 it’s unethical as hell 2 it’s illegal I don’t want to go to jail. 3 I’m learning cyber security NOT hack stuff because someone hurt your useless feelings.
Ohhh and they always get pissed off when I explain everything wrong with their idiotic request10 -
So this just happened. Some background before I begin: We're understaffed, my desk is in the back of the building, and there's no one really at the front to greet people. No security either...
Guy walks in wearing a flannel jacket (no shirt under it), pajama pants, and sandals. He looks like hell. Explains he was just released from a hospital and his apartment is locked. I let him use my phone to call his sister.
When I talk to his sister, she barely wants to speak with him. Tells me his apartment is locked for a reason and he's not allowed back. I'm just like: "So... what would you have us do for him?" At this point if his sister won't help, I was going to ask him to leave. Oh, and that hospital was a drug rehab.
So it ends with him waiting for a ride, but he ends up napping on the couch in the front of our office. CEO/Owner and his business partner walk right past and say nothing. They go into a meeting. I'm trying to figure out if I ask him to leave, wait outside for his ride... I'm a developer, this isn't my job.
A good 45-60 minutes later, after the guy walked outside and then came back in and laid back down on the couch, he leaves with his ride. Shortly after the owner walks out of his meeting, so I ask him what to do in this situation - more hoping he'd realize the need for more security.
If this story isn't crazy enough, the business partner pipes up - absolutely serious - and says he didn't say anything because he thought the guy was a developer.
So I've learned that we've got extremely low hygiene standards for developers here, with a relaxed dress code and are allowed nap times on the front couch.
Thankfully our CYBER security is better than our PHYSICAL security. :|1 -
Please stop putting critical infrastructure to the internet. Security on the internet is a joke, and we won't be laughing the time when someone dies from a cyber attack on another pipeline/dam/weapons factory.17
-
THE CODE USED IN MY MANDATORY ONLINE TRAINING ABOUT CYBER SECURITY AND STUFF LIKE THIS:
<script>window.showQuestion(someOverlyVerboseResponseFromTheServerWithTheCorrectAnswersMarked);
</script>
Oh boi it would be a real shame if someone proxied your precious function :)2 -
Our local cyber security team has asked all to remove docker from their laptops, reason they can't track them
Most of our stack is aws fargate with nodejs and java springboot
Developers = wtf ?!!1 -
Well, here is another Intel CPU flaw.
I'm starting to think that all these were done on purpose...
https://thehackernews.com/2019/05/...3 -
Anyone who's interested in cyber security, go follow Binni Shah (@binitamshah) on Twitter. The amount of tutorials and guides she retweets is crazy and very informative.
Also if you're not on Twitter you're missing out on a lot of content to learn from ✌️18 -
I find it hilarious the total misconception of hacking that the general public has. I tell people I know cyber security (Not as much as a lot of people around here) but it is a hobby of mine and I find it very useful/interesting.
But I can't stop but laugh when someone is like, can you get all the text messages my bf receives?
Can you hack this for me can you back that?
C'mon even if I knew how to do that without being caught you think I would even admit that to you. Do hackers just walk around with an index card pasted to their forehead of their skill? It's not even slightly reasonable to think this lol even for someone who doesn't know about the field -
Comment a 1 if you’re a web dev.
Comment a 2 if you’re a game dev.
Comment a 3 if you’re a data scientist.
Comment a 4 if you’re in cyber security.
Comment a 5 if you’re in IT.
Comment a 6 if you don’t fit any of the above categories and you code only in PHP and refuse to learn any other language because you think PHP is the future.50 -
OKAY BUT WHY THE FUCK DO PEOPLE HAVE TO ACT LIKE THEY'RE SOME KIND OF GOD WHEN THEY CAN'T EVEN PASS AN INTRO CLASS. Some background: I go to an early college in high school program which offers computer science where you take two college classes a semester starting you junior year in high school. AND THIS GIRL TALKS ABOUT THIS PROGRAM LIKE IT'S AWFUL AND SHE HATES IT AND HOW THE PROFESSORS DON'T TEACH AND SHE FAILED AN INTRO TO PROGRAMMING CLASS WHICH TEACHES JAVA BUT THEN SHE ACTS LIKE SHE'S WAY ABOVE THE OTHER KIDS IN MY CLASS BECAUSE SHE'S RETAKING IT. SHE'S ALSO A STUDENT ASSISTANT IN MY CYBER SECURITY CLASS BUT DOESN'T KNOW WHAT THE localhost IP IS. I UNDERSTAND THAT I DON'T KNOW EVERYTHING BUT AT LEAST I DON'T ACT LIKE I DO. IT'S SO INFURIATING!!!!!!
-
Just heard this on the news...
"The cyber security on my smart phone compared to the cyber security in medical equipment..."
Wtf did I just hear??? I mean, I get it...using terms the general public understands... But how about educating people instead. 😤1 -
Many people / engineers around me talk about trendy stuff like Cybersecurity or AI and show off what great encryption and neuronal networks they 'have built' ( I would rather say 'using').
I kinda get the feeling of 'Everbody talks about it - no one really knows what's goin' on inside (especially those guys who hate math and even algorithms).'
Am I just stupid or does somebody else here feel the same way? I mean people have been doing serious research about this stuff for years. And currently many kids are coming up with it as if it is easy stuff like the bubble sort.4 -
Had my first interview for a cyber security gig.
1st round, preliminary questions about ethics in a security related topic, etc.
I wrote a report about that topic, but for some reason brain fogged the answer.
At the end of the interview, I also blurted out that I found the interviewer's presentation at a past conference and really liked it.
Pretty sure they now think I'm a creep.
That being said, it's been a few years since I've interviewed, so it feels great to get the dust off, even if I bombed it
Practice makes perfect, right?!2 -
Learn about
-Cyber Security
-Machine Learning (especially Reinforcement Learning & GANs)
-Microcontrollers (ATtiny)
Of course I want to finish the projects I'm currently working on and maybe start a YouTube channel about my projects.
Yes I know, it's quite a lot to do, but I don't know if I will ever have the chance to do all that things in my free time again. -
whenever i tell my dad about a technology that is going way beyond our imagination and tell him about the consequences of it and how we should worry about that
then he watches some random tv show about internet security/cyber security and various algorithms (very abstract) which are currently changing the world and how we should care about our data and what the consequences of X technology is...
he be like: "oh is that true? that's interesting, how does that work?"
i'm like😑 dad, i already told you about that😩
ever had similar experience?1 -
What's a good book to read about hacking and/or cyber security? Doesn't have to necessarily a how-to guide, rather, just something to read on the subject.5
-
My first job was writing a cloud based malware analysis system from scratch for UTSA's Institute for Cyber Security.
My direct supervisor was a womanizing, lazy, prick with a PHD. I wonder where he is now.3 -
Never been a fan of podcasts before, but I'm fixing to take a stab at listening to some.
What's a good tech/programming podcast? (Bonus points if it's about Cyber security) -
Anybody else feel like their Internet traffic constanty being monitored after downloading pen testing tools?
Have our identities been added to lists of potential cyber criminals :/
Thoughts?
(For ethical purposes - involving your own site's security!!)2 -
When in an application security talk put on by our cyber security department and one team (not mine) is being chastised for only doing client side validation, another dev asks so at what point can we trust the user? A few people nod and indicate they want an answer, and the speaker, said never, you never trust the user.
I can't believe people can graduate and get a job and keep a development job, especially in a highly government regulated company like where I work2 -
!rant
I'm a computer engineering student.
I'm very much interested in Systems and networking.
That's why I was thinking of persuing cyber-security as a career option.
But I'm not quite sure if that is a good choice.
Also I don't know how to proceed in order to achieve excellence in cyber-security.
It would be a great help if you guys could help me.
Thanks :)20 -
Honestly, school is useless for me as of right now. I know I should be well rounded and stuff, but do I honestly need to know the symptoms of cervix cancer while going into a tech career? My eyes have been set on tech for my whole life, ever since I left the womb, and I know that if I do switch careers, it'll be from comp sci to cyber security not from IT to med school...
I feel like I could really be devoting my time towards something better than writing a 5 page essay on a healthy food choice.
Every night I think to myself, "You know what, I'm going to lock myself in a room and write bash scripts all day" but then I wake up in the morning, and remember I have to take a quiz on reproductive systems, learn about the procedure of organ donations for driver's ed, write 2 paragraph definitions of vocab words, and read a book about communism.
The most useful thing I learned last year, was how to efficiently navigate the java API, and that's something you don't even learn, you just encounter it. Schools need to start having more specific specialties and stop enforcing knowledge of pointless topics.
I'm not saying to remove all core classes and stuff, I'm saying why waste space in our brains with something we won't use ever again? I get it, some people don't know what career they're looking for yet so you can't make them choose, but it honestly sucks some serious ass that I can't learn what I want to at school, and as a matter of fact, I can't even learn at home, because they're filling my schedule with pointless work because they feel that they have to fill our time somehow.
Point of this long ass rant is: Why lock yourself in a room and learn about something if it isn't something you want to learn about? The space in our brain is finite enough, why can't it be filled with things we're interested in rather than things that will only be used to get good grades in the future then overwritten with useful knowledge. Same thing with time. We have a very finite amount of time in a day, and now that I think of it, a lifetime. Why spend it on something that doesn't, and never will, make your life enjoyable?3 -
*Has more advanced knowledge on computers and cyber security...
Mother still cant trust with repairing phone, asking which phone to buy, and naggs about the amount of time i spend on my laptop saying i'd break it. -
Pretty sure someone else said it before but: chose something else.
The market is over saturated with developers. There are plenty of other spaces in which you can work with computers and code.
Think: system administration, cyber sec (which also pays higher in a lot of places compared to development since resource security is a priority), networking etc.21 -
Pentesting for undisclosed company. Let's call them X as to not get us into trouble.
We are students and are doing our first pentest at an actual company instead of assignments at school. So we're very anxious. But today was a good day.
We found some servers with open ports so we checked a few of them out. I had a set of them with a bunch of open ports like ftp and... 8080. Time to check this out.
"please install flash player"... Security risk 1 found!
System seemed to be some monitoring system. Trying to log in using admin admin... Fucking works. Group loses it cause the company was being all high and mighty about being secure af. Other shit is pretty tight though.
Able to see logs, change password, add new superuser, do some searches for USERS_LOGGEDIN_TODAY! I shit you not, the system even had SUGGESTIONS for usernames to search for. One of which had something to do with sftp and auth keys. Unfortunatly every search gave a SQL syntax error. Used sniffing tools to maybe intercept message so we could do some queries of our own but nothing. Query is probably not issued from the local machine.
Tried to decompile the flash file but no luck. Only for some weird lines and a few function names I presume. But decompressing it and opening it in a text editor allowed me to see and search text. No GET or POST found. No SQL queries or name checks or anything we could think of.
That's all I could do for today. So we'll have to think of stuff for next week. We've already planned xss so maybe we can do that on this server as well.
We also found some older network printers with open telnet. Servers with a specific SQL variant with a potential exploit to execute terminal commands and some ftp and smb servers we need to check out next week.
Hella excited about this!
If you guys have any suggestions let us know. We are utter noobs when it comes to this.6 -
Has anyone used python within cyber security?
I really want to get into cyber security. I'm curious what programming languages are used within that industry.4 -
How did you learn cyber security, especially pentesting ?
I know that making VM lab and/or doing CTFs and reading writeups can help a lot, but is there any more "formal" way to get into things like pentesting etc. ?
(Without having to pay for OSCP, Sans and all this)5 -
I chose Network/Cyber Security because it was my internship experience and they were willing to pay me good money to stay on... No but seriously I am much better at understanding how complex systems work than coding them. This job, as stressful as it is, is a different kind of stressful that the deadline-fraught jobs of software developers worldwide.
And i can do it fully remote.2 -
I take a moment for myself and assess the situation from a bird's view.
Then, I objectively look at the current situation and my response/reaction to this and try to change my thinking process/acting to a more rational one.
But, also, my general way of thinking in the cyber security world plus how I'm hardwired to think in a 'paranoid' kind of way makes my current job so fucking perfect for me that i often think about that and the fact that there aren't many people around who have this.1 -
Laziest habit? Anything done between 1pm-4:30pm and 4:59pm-8pm. During that time, habits include unnecessary refactoring, poking the CI/CD containers, editing already made prototypes in gimp inkscape, pasting stackoverflow topics to youtube, bouncing from macOS, windows and kde distros in search of zen/rice, adding a calendar emoji on my slack :), making useless automation scripts, building on every variable's value change, tinkering pixels, shades, gradients (and their angles), dimens, anim values, anim curves, opacity, blurs and just nuking the ui just to copy paste an old one, 60% just chatting in code alongs, changing key bindings (from ide to OS), and ultimately zoning out on a podcast about cyber security. And of course: waiting for ++ and comments
-
Hey,
Any tips on how to apply for job, I apply to 10-15 new opportunities daily but haven't received positive response from 99% of them. I don't know what's wrong.
Currently, I am a cyber security analyst at a startup since February 2023.
My resume I use to apply for job
https://ganofins.com/ganesh-bagaria...21 -
is there some trendy definition for "keyboard pattern" that im unaware of?
seriously though... while not always current on whatever scammer\phisher\wannabe hackers\etc are doing... im still one hell of a, beyond capable, cyber security pro... mainly cuz I've been networking professionally since half-duplex existed, know, and thoroughly enjoy data architectures, encryption and things like hardware drivers and low level systems down to the literal, physical\mechanical and digital bits...
basically,i have a rare viewpoint in comprehension; I'm used to nonsensical tactics being enforced as if they were actually valid (basically everything other than a min length (~6+) and *don't use basic words found in a pocket dictionary* is typically a double edged sword).
so wtf do they mean? i mean, technically, everything typed can be a keyboard pattern... itd be like how people say "vps" when they are talking about a proxy. 19
19 -
So first time here seems awesome I'm an aspiring cyber security expert I know very basic c++ and I'm looking for people to talk to about what I should be doing5
-
Hey everyone. I am a freshman in college studying Cyber Security. I have been practicing various programming languages such as httml, css, java script and SQL. Does anyone have any recommendations for resources to study? My end goal is to be blue teaming for my schools Cyber Defense team in the fall.5
-
Okay so, I’ve recently started going through our products’ security postures and their teams’ related practices and processes. I knew things were in a bad state, but I have to admit I’m a bit anxious at how bad things are… and it’s not like nobody cared or anything, quite the opposite; the teams are quite motivated about cyber sec. It’s just that they don’t know what the fuck to do and where to start even if they did.
Okay, that’s my job to figure out the roadmap to improving their security posture and processes and help them implement it. If it wasn’t bad enough that there’s half a dozen products whose cyber sec roadmaps I need to prioritise and manage somehow, I heard this week that due to some organisational rearrangements, the number of products under my stern guidance will nigh on double at some point very soon…
I need a team. Give me a team.2 -
So I went to a car repair center and asked if they could fix my bike. They said they could but they won't. This is outrageous, obviously a bike is less complicated than a car and they can actually fix it, they just won't because it's "not their job". Unbelievable!
//This didn't really happen of course
//people don't think this is acceptable, but if I won't fix their laptop they are surprised and act the same way. I study ICT (embedded software engineering and cyber security, but they don't understand that so ICT it is) so I HAVE to fix their laptop....
//Non-techies should really learn that just because we can do something, we don't have to do what they ask of usrant hi linuxxx fuck people repair unrealistic expectations stupid people we don't have to laptop hi -angry-client-11 -
Just had a so called "cyber security" seminar in college today.
The guy who claimed to be a trainer or somewhat network security guy or something behaved enigmatically with utter consistency. He obviously claimed to know facebook hax0ring though.
They were basically there to advertise their complete crap: csksrc.org
(Ethical Hax0ring Course) (also claimed their site to be 99.9% secured - GREAT!)
After obtaining a ISO*** standard cert or after taking multiple sessions on "advanced ethical hacking" if you go about telling peeps in colleges that: "The single way to hax0r a facebook account is CSRF!" "Will hack your facebook account by MITM through malicious WiFi Ap." Then, NO neither I want your shitty cert nor do I want to be in your team and create the next level of "advanced ethical hax0ring - CEH course". Reason why I get cringed when peeps start about their certs and the ISO*** value it contains. What ISO value does your brain cells contain though? -
Question - my field is information security (or cyber security if you want to think of me as a time lord), but I wanted to know;
Front end and back Devs, how much time do you spend on security issues and/or implementing security measures?9 -
Typical insurance company BS approach.
Listening to xmas music, Spotify ad kicks in about 'just being "hacked"':
Buy our cyber security insurance product to quickly recover and retain liquidity in case of a cyber security beach.
Not a single word about preventing the incidents in the first place...
Lucky to work in a place that doesn't skimp on IT.3 -
So I just got the cyber security pack on humblebundle... $15 for a year of PIA, a year of spider oak one cloud backups and a year of Dashlane are the notable ones (I’ll give away the antivirus ones for free since I don’t have windows).
But that wasn’t the awesomest part...
I installed Dashlane and after transferring all my stuff over from LastPass, I went to delete my LastPass
Dashlane autofilled the username...
It’s like so subtly aggressive in an unintentional way. Honestly this password manager Battle Royale is totally worth the $15 regardless.13 -
Any of us had annoyances with people with “a million dollar app idea” but what about these which gives unsolicited career advice?
I’m dealing with a boomer which keeps trying me to change my career and work into cyber security (because TV told him it’s a well paid field) despite me kindly telling him for multiple times which it’s not going to happen because I won’t throw away a career I love to work in a field which seems deadly boring to me (I love anything about coding from design to typing for hours on Vim meanwhile the only thought of reading for hours obscure documentation to find potential vulnerabilities on a system kills my spirit).7 -
🚀 *iBOLT CYBER HACKER: Cryptocurrency Recovery & Advanced Hacking Solutions!* 🦊💻
🔐 *Lost access to your crypto wallet or had your funds stolen?* Don’t worry— iBOLT CYBER HACKER is here to help you recover your cryptocurrency with cutting-edge technical expertise.
💡 With years of experience in the crypto world, iBOLT CYBER HACKER employs the latest tools and ethical hacking techniques to help you recover lost assets, unlock hacked accounts, and retrieve funds from inaccessible exchanges.
⚡ Whether it’s a forgotten password, an accidental transfer, investment scam, or a major security breach, iBOLT CYBER HACKER has the expertise to help you get your crypto back.
- General phone hacking and monitoring
- Money recovery from scammers
- Bitcoin and PayPal recovery
- Mobile phone monitoring
- Hacking and modifying university grades
- Bank website hacking and fund transfers
- Database hacking with admin privileges
👉 *Contact iBOLT CYBER HACKER for professional assistance
📧 𝐄𝐦𝐚𝐢𝐥: Support @ibolt cybarhack. com
𝐨𝐫
📲 𝐖𝐡𝐚𝐭𝐬𝐀𝐩𝐩: +39, 351..105, 3619
http s:// ibolt cybarhack. com1 -
I'm a bit frustrated. I'm 23 and I finished a Bachelor's Degree in Computer Engineering last 2015. Working on a career path in cyber security. Is it normal to just understand and test the concepts and not fully memorize everything? It really bothers me that I feel I don't know anything despite developing small tools, testing other people's work, reading about related topics and playing with Kali.5
-
Looking at colleges on summer break between learning python and some projects can't decide between computer science and cyber security as a major 😰 why can't I choose2
-
I think the thing that sucks about high school (or school in general, really) is that they don't really have many opportunities for the people that like to program or do anything with computers.
The only classes that have to do with computers at all (In my high school) is Intro to Programming (Which is what I'm taking, which has HTML, CSS and JavaScript), some computer science classes and finally the Cyber-patriot team. (Which is for Navy ROTC and it consists of Cyber Security, competitions and actual Linux computers).
The only few of eight classes I find actually interesting is Intro to Programming, NJROTC, and Plant Science. (Because not only the subjects, but the teachers (and Sergeant) actually make it fun, interesting and easy to understand, while the rest don't feel like they're doing a good job.)4 -
I recently joined DevRants, and with me joining any new site or media where you can share I am usually the guy who is shy and likes to sit back and watch/read. However I wanted to post a question as I am trying to get a job within the Cyber Security field. I have a computer science degree and honestly I feel like I can't even code at a level I should be able to. I am also currently working/studying for my CompTIA Security+. It has been going good but, I always second guess myself and doubt my abilities. I guess this a a slight rant and question so far.
My question is how can I better improve both my skills (coding, linux, and security) and also my mental. I would say its imposter syndrome but I don't have a job so I don't think it would be fair to say it is. I just want to break into the job field and show people that if given the help and resources I can excel at the task given. I do learn fast and pick things up pretty good. Any help/recommendations is much appreciated, and I look forward to more talks.2 -
/*
No Rant
*/
anyone here with a cyber security cert? i kinda want to go that route of cyber securty. so im curious if its worth it.12 -
I'd love to get into a career within the cyber security industry.
Anyone got advice?
I've played around with Kali/Parrot and setup a proxmox box to perform pen testing and have a fair number of PDF ebooks and audio books on networks, security and pen testing12 -
Discord server under development for software engineering, cyber security, networking, and IT talk in general. Looking to meet new people and talk :). @ me if you're interested in testing it.4
-
Hey guys, I want to do a cyber security career. For me it's the most interesting field in CS. How can I get started? Is it worth to do some online courses where you get certifications (asking this because they are kind of pricey). I'm a QA Tester with 1 year of work experience, don't know if I should just apply to jobs or acquire skills/certificates first. Thanks for all the incoming answers. :D5
-
Some competitions are so unorganized.
So me and my team went for this national level technical paper presentation competition. Our topic was a cyber security topic and they put us under Mechanical branch even though I had informed them about this discrepancy two weeks back. Apparently the girl whom I complained to wasnt on the organising committee although she was the one who was promoting this competition in the first place. Sheer irresponsibility!!3 -
I am learning cyber security, the weird thing is, 90% of the times i find theory in lectures...so less practical content is present, even then web sites like tryhackme provide work machines which are next to use less if you dont pay for a subscription...FML!4
-
How does someone with. A+ certs and a Network + and Cyber Security certifications and still only getting Help Desk jobs calling them 🤷♂️2
-
So hypothetically I have a friend who wants to get a job in cyber security but has no formal education or means to afford one, at the moment. He knows enough about computers to navigate and execute most common tasks, and certainly has the drive, common sense, and brains to succeed but can't afford to in this almost cutthroat field...
How would he begin to teach himself?
He has a laptop, Kali Linux, The BTFM and RTFM books, The Hacker's Playbook 3; and the internet.
Make his day with your two cents.1 -
Why do most people think that a person can only be great at one thing.
I've just started working as a developer and when I tell people I am also learning cyber security they are like what's the point of it. And how I should focus on one thing and blah blah.
Man, nobody questions Elon Musk when he is learning new things everyday. But then why can't we do the same and man we don’t need to be judged. A little support would be so much better.6 -
Whatever be the current trend on Linked-In, at the end of the day the product development life cycle remains quite the same.
Still, as developers which general domains in software do you think would flourish in the near future?
My picks (not in order) -
>> Cyber security : automation, both offensive and defensive
>> Block chain : trustable data platforms
>> Applied AI : a few key models, applied to all niches, bettering existing UX
>> IOT : wearables, embeddables, smart appliances
>> AR : Navigation prompts, real time info about real life objects
>> VR : Immerse entertainment. (Metaverse 🤮)
>> Quantum computing : first gen costly commercial releases, new algos
What would you add or subtract from this?1 -
Recovering Investment Losses with GearHead Engineers Cyber Security Services
In today’s increasingly digital financial landscape, investors face growing threats from cybercriminals targeting everything from brokerage accounts to blockchain-based assets. For individuals and businesses alike, falling victim to a cyberattack or financial scam can be devastating. Fortunately, firms like GearHead Engineers, known for their advanced cybersecurity services, are stepping in to help investors recover losses and, more importantly, prevent future breaches.
The Rise of Cyber-Investment Threats
As digital platforms have become the norm for managing investments, they’ve also become a prime target for hackers. Common threats include:
* Phishing scams that trick users into revealing login credentials.
* Ransomware attacks on financial firms.
* Malware that siphons personal and financial data.
* DeFi and cryptocurrency hacks exploiting insecure smart contracts or user wallets.
The financial implications can be enormous, especially when assets are stolen, trading accounts are compromised, or confidential investment strategies are exposed.
GearHead Engineers: A Cybersecurity Partner for Investors
GearHead Engineers specializes in protecting financial data, systems, and transactions with comprehensive cybersecurity strategies tailored to modern digital investment environments. Their services include:
* Threat Detection & Response: 24/7 monitoring of systems to identify unusual activity before it becomes a serious threat.
* Incident Forensics: In the event of a breach, GearHead Engineers conduct thorough investigations to trace the source, identify vulnerabilities, and assist in recovery efforts.
* Asset Recovery Support: While not a financial firm, GearHead can coordinate with law enforcement and digital forensics specialists to trace stolen digital assets, especially in cryptocurrency-related incidents.
* Security Audits & Penetration Testing: Preemptive testing of platforms and networks to find and fix security holes before hackers do.
* Cyber Insurance Advisory: Guidance on cyber insurance coverage and how to maximize your protection and potential reimbursement in case of a loss.
Real-World Application: Turning Loss into Learning
Clients who’ve suffered financial loss due to cyber incidents often find that working with cybersecurity experts like GearHead Engineers is a turning point. Not only can the firm help assess whether any funds are recoverable (especially in crypto and digital asset cases), but it also strengthens the client's defense moving forward.
By implementing robust firewalls, multi-factor authentication, encryption, and behavioral analytics, GearHead Engineers empowers investors to take control of their digital financial security.
Conclusion: Proactive Security is Smart Investment Strategy
Recovering from a cyberattack is never easy, but it’s possible—especially with the right partners. GearHead Engineers brings a unique blend of technical expertise and practical support to help victims of cyber fraud bounce back and secure their future. For investors, engaging in strong cybersecurity isn’t just risk management—it’s a smart investment in itself.4 -
Not sure how to ask this. I really enjoy Network side of IT. Maybe even throw in a little Cyber Security as well. I feel like I'm trying to every too fast. I got no certifications yet. This is stressful 😫1
-
I'm looking for a project idea in cyber-security...
Any ideas?
I'm good with x86 assembly, c, c++, python and shell scripting.
I'm very well versed with Linux operating systems and basic networking stuff.
I'm willing to learn new concepts11 -
Happy Friday. Facebook just disclosed hackers have exploited multiple vulnerabilities to get access to potentially 50 million users. I guess... no weekend for the blue team? https://mobile.twitter.com/dnvolz/...
-
I'd like to one day work on security consulting/advising (incident response, opsec, SOC, etc). For those of you here that are currently in or have worked with people in that field: what advice do you have for handling cyber risk situations?1
-
Where I learn networks and cyber security, we started working with Scapy. I have a problem with pycharm, it cannot resolve half of Scapy's functions. Do any of you know how you fix it (the program runs but pycharm still doesn't like it)3
-
HIRE A CRYPTO RECOVERY EXPERT; CYBER CONSTABLE INTELLIGENCE YOUR ULTIMATE SOLUTION FOR LOST CRYPTOCURRENCY
I am truly at a loss for words as I try to express my deep gratitude to Cyber Constable Intelligence for the incredible support they provided me during one of the darkest times of my life. I never imagined I would find myself in a situation like this, but I am so thankful I reached out to them when I did. A while ago, I became desperate to access my spouse’s phone, as I had suspicions about his conversations with another woman. In my search for help, I made the terrible mistake of trusting a hacker who claimed they could assist me in gaining access. Little did I know, this hacker had ulterior motives and would take full advantage of my vulnerability. Instead of helping, the hacker scammed me, taking a significant amount of my Bitcoin, and even worse, he blackmailed me. He threatened to expose my personal information and demanded more money from my spouse. I felt completely trapped, unable to think clearly or find a way out. It seemed like I had lost everything my money, my peace of mind, and even my sense of security. That's when I found Cyber Constable Intelligence. After reading about their success stories, I decided to reach out, even though I was unsure what to expect. From the moment I contacted them, I felt a weight lift off my shoulders. They listened to my situation with empathy and immediately got to work, providing not just technical expertise, but the reassurance I desperately needed. Thanks to their diligent efforts, they were able to track down the hacker who had caused me so much distress. Not only did they help me recover all of my lost funds, but they also made sure the hacker was held accountable for his actions. In addition, they helped me gain access to my spouse’s phone, revealing the truth behind his communications with the other woman. I am incredibly grateful to Cyber Constable Intelligence for their dedication, and compassion. They went above and beyond to help me recover both my finances and my peace of mind. If you find yourself in a similar situation, I highly recommend reaching out to them. They truly saved me, and I will always be thankful for their intervention.
Here's Their info below
Website Info : www cyber constable intelligence com
Email Info: cyberconstable (@) coolsite net26 -
BEST BITCOIN RECOVERY COMPANY |CRYPTOCURRENCY RECOVEY HIRE CYBER CONSTABLE INTELLIGENCE
One evening on a Friday after work, I found myself in a terrifying situation. I had just finished a long week and was looking forward to unwinding over the weekend when I decided to check on my cryptocurrency holdings. To my horror, I discovered that my XRP had become trapped on a cryptocurrency exchange called Crypto change, which I later realized was operated by scammers. Crypto change had always seemed like a reliable platform, but now, under strict geopolitical restrictions, it had suddenly become impossible to access my funds. Every attempt to withdraw my XRP was blocked, and I was left helpless, with no way to recover my assets. The value of my XRP had grown to over $100,000, and the thought that it might be permanently out of my reach was overwhelming. Panic set in as I realized I had fallen victim to a fraudulent exchange, and all of my usual recovery methods seemed useless. Desperate for a solution, I reached out to Cyber Constable Intelligence, a firm known for its expertise in Cryptocurrency Recovery. I didn’t know what to expect, but I was willing to try anything at that point. From the moment I contacted them, I felt a sense of relief. The team at Cyber Constable Intelligence sprang into action immediately, understanding the severity of my situation. They knew that Crypto change wasn’t just an exchange with withdrawal issues, it was a scam designed to trap unsuspecting investors like me. However, they assured me they had the skills and experience to navigate this challenging scenario. The experts at Cyber Constable Intelligence quickly identified vulnerabilities in Crypto change's KYC (Know Your Customer) processes, weaknesses that the scammers had overlooked. They put together a detailed plan to exploit these gaps, enabling them to move my XRP to a secure wallet, bypassing the scam exchange’s restrictions. It wasn’t an easy task. The process took several weeks of careful, discreet work. The team had to balance security measures while avoiding detection from the exchange’s administrators. Throughout the recovery, I was kept informed of their progress, and their dedication was evident. In the end, their efforts paid off. My XRP, valued at $100,000, was safely moved from Crypto change to a secure wallet under my control. Thanks to the relentless effort and expertise of Cyber Constable Intelligence, I regained access to my trapped funds. The professionalism and skill they displayed in handling my case were extraordinary. I can now breathe easy, knowing my investment is safe, and I owe it all to their exceptional service and dedication.
Here's their Info below
WhatsApp: 1 252378-7611
Website info; www cyberconstableintelligence com
Email Info cyberconstable@coolsite net
Telegram Info: @cyberconstable1 -
LOST BITCOIN & OTHER CRYPTO ASSETS WITH DUNAMIS CYBER SOLUTION
One Tuesday evening after work, I received a friend request on
Instagram from someone named Jason. His profile seemed genuine well-dressed, professional-looking, with a few mutual followers. I accepted without thinking much of it.Jason started engaging with my posts right away, liking photos, leaving kind comments, and eventually messaging me. He was charming, respectful, and attentive. Over the next few weeks, we built a connection. He told me about his work in online trading and how it had changed his life. He seemed successful and confident, and honestly, I was intrigued.Eventually, he offered to teach me how to trade. He explained everything step by step, sending voice notes, videos, and even walking me through the platform he used. He said he wanted to help me become financially independent. It felt like he genuinely cared. The platform he introduced me to looked professional, and with his guidance, I started making what appeared to be real profits.I began with a small investment, and the returns came fast. Jason encouraged me the entire way, helping me manage trades and explaining strategies. Seeing my account balance grow gave me confidence, so I kept going. Over time, I invested more and more, eventually totaling $220,000.Then, everything changed. When I tried to withdraw my funds, they said I had to pay a processing fee. Then another. Then the platform claimed there were security issues. Jason became distant, then stopped replying altogether. The platform eventually disappeared. That’s when it hit me I had been scammed.I was crushed. But after hours of researching, I found DUNAMIS CYBER SOLUTION. I was hesitant at first, but I reached out. To my surprise, their team responded quickly. They were understanding and incredibly skilled. They took immediate action, investigating the scam and tracing the digital trail.Through their cyber tools and expert recovery process, they tracked down the operation behind the fake trading platform. Within weeks, they were able to recover every single dollar I had lost.DUNAMIS CYBER SOLUTION didn’t just save my money they saved me from the worst financial mistake of my life. If you’ve been scammed, please don’t give up hope. Contact DUNAMIS CYBER SOLUTION. They’re 100% genuine.
d2 -
Hire the Best Cryptocurrency Recovery Expert / Captain WebGenesis
If you're feeling overwhelmed and frustrated by the loss of your hard-earned money, fear not! Contact CAPTAIN WEBGENESIS CRYPTO RECOVERY CENTER today and let him work his magic in recovering what is rightfully yours. With years of experience in the field of cyber security and financial fraud investigations, CAPTAIN WEBGENESIS CRYPTO RECOVERY CENTER is a trusted expert who has helped countless individuals reclaim their lost funds. His dedication to assisting those in need, coupled with his unparalleled knowledge and skills, make him the perfect ally in your quest for justice. So why wait any longer? Take control of your financial future and reach out to Captain WebGenesis today – he's ready and excited to help you get back on track!
Call or SMS, +1(501)436-9362
Email Add; Captainwebgenesis@ hackermail. com2 -
Unlocking My Crypto Wallet: A Breakthrough with Morphohack
A crippling sense of loss had taken hold of me. My seed phrase, the key to unlocking my cryptocurrency wallet, had vanished. Every attempt to recall it had failed, and I'd resigned myself to losing access to my digital assets forever.
A spark of hope flickered to life when I discovered Morphohack Cyber Service through a colleague that works for my tech firm, a pioneering crypto recovery firm renowned for their seed phrase recovery expertise. Their team of specialists possessed the technical wizardry to salvage lost digital treasures.
With newfound optimism, I entrusted Morphohack with my predicament. Their experts methodically guided me through a meticulous process, ultimately leading to the successful recovery of my seed phrase.
As I regained control of my cryptocurrency wallet, an immense sense of relief washed over me. Morphohack's exceptional prowess had salvaged my digital assets, restoring my faith in the security of my investments.
If you're struggling to recover your seed phrase or access your crypto wallet, Morphohack Cyber Service is a trustworthy ally to have by your side. You can reach out to them at [E-mail: Morphohack@Cyberservices . com, WhatsApp: +1 213 672-4092,]
Their expertise and guidance can help you unlock your crypto wallet and regain control of your digital assets.1 -
ToyStack Virtual OS - A secure, cloud-based virtual OS that works on any device—no installation required, fully customizable, and always accessible.
ToyStack Virtual OS redefines virtual desktop computing by offering a secure, scalable, and high-performance cloud-based operating system accessible directly through any web browser. Eliminating the need for traditional software installations, ToyStack’s agentless approach simplifies deployment and reduces hardware dependency—cutting costs while enabling seamless access to workspaces from anywhere in the world.
Designed with enterprise-grade security at its core, ToyStack Virtual OS integrates multi-factor authentication (MFA), end-to-end encryption, and AI-powered threat detection to safeguard sensitive data. It adheres to globally recognized compliance standards, including ISO 27001, 27017, 27018, and SOC 2 Type II, ensuring protection against evolving cyber threats and regulatory requirements.
Flexibility is at the heart of ToyStack’s design. It supports Windows, Linux, and custom operating systems, all managed through a centralized Control Tower. This intuitive management console enables IT administrators to enforce group policies, streamline user provisioning, and monitor performance—all in real-time. Whether managing hybrid teams, remote workforces, or distributed operations, ToyStack adapts effortlessly to dynamic business needs.
Performance is never compromised, thanks to AI-driven resource optimization that intelligently allocates computing power based on workload demands. This ensures zero-lag experiences and seamless scaling during peak usage, empowering teams to remain productive without interruptions.
Beyond performance, ToyStack Virtual OS drastically reduces IT overhead and operational complexity. Built-in automation handles provisioning, updates, and security enforcement, minimizing administrative burdens. With its pay-as-you-go pricing, businesses can avoid costly licensing fees and infrastructure investments, making it a cost-effective alternative to traditional Virtual Desktop Infrastructure (VDI).
Whether you’re scaling operations globally, enabling BYOD policies, or enhancing remote work security, ToyStack Virtual OS delivers an unmatched combination of simplicity, security, and performance—future-proofing your organization for the modern digital workspace.5 -
Weddings are supposed to be magical, but the months leading up to mine were anything but. Already, wedding planning was a high-stress, sleep-deprived whirlwind: endless details to manage, from venue deposits and guest lists to dress fittings and vendor contracts. But nothing-and I mean, nothing-compared to the panic that washed over me when I realized that somehow, I had lost access to my Bitcoin wallet-with $600,000 inside. It happened in the worst possible way. In between juggling my to-do lists and trying to keep my sanity intact, I lost my seed phrase. I went through my apartment like a tornado, flipping through notebooks, checking every email, every file-nothing. I sat there in stunned silence, heart pounding, trying to process the fact that my entire savings, my security, and my financial future might have just vanished.
In utter despair, I vented to my bridesmaid's group chat for some sympathetic words from the girls. Instead, one casually threw out a name that would change everything in a second:
"Have you ever heard of Tech Cyber Force Recovery? They recovered Bitcoin for my cousin. You should call them."
I had never heard of them before, but at that moment, I would have tried anything. I immediately looked them up, scoured reviews, and found story after story of people just like me—people who thought they had lost everything, only for Tech Cyber Force Recovery to pull off the impossible. That was all the convincing I needed.
From the very first call, I knew I was in good hands. Their team was calm, professional, and incredibly knowledgeable. They explained the recovery process in a way that made sense, even through my stress-fogged brain. Every step of the way, they kept me informed, reassured me, and made me feel like this nightmare actually had a solution.
And then, just a few days later, I got the message:
"We have recovered your Bitcoin."
(EMAIL. support @ tech cyber force recovery . com) OR WHATSAPP (+1 56 17 26 36 97)
I could hardly believe my eyes: Six. Hundred. Thousand. Dollars. In my hands again. I let out my longest breath ever and almost cried, relieved. It felt like I woke up from a bad dream, but it was real, and Tech Cyber Force Recovery had done it. Because of them, I walked down the aisle not just as a bride, but as someone who had dodged financial catastrophe. Instead of spending my honeymoon stressing over lost funds, I got to actually enjoy it—knowing that my wallet, and my future, were secure. Would I refer to them? In a heartbeat. If you ever find yourself in that situation, please don't freak out, just call Tech Cyber Force Recovery. They really are the real deal.1 -
Crypto Scam Recovery Company; How To Recover Lost Bitcoin If It's Stolen| Hire CYBER CONSTABLE INTELLIGENCE
An "investment mentor" promised to teach me flash loan arbitrage strategies, which sounded intriguing and potentially profitable. Eager to learn, I followed their instructions and connected my wallet to what I believed was a legitimate crypto dashboard. The interface looked professional and convincing, mimicking real platforms I had seen before. However, I was completely unaware that this was a fake site designed to deceive unsuspecting users like me. By connecting my wallet to this fraudulent dashboard, I inadvertently granted unlimited spending approval. This was a critical mistake that would cost me dearly. In a matter of seconds, the scammer executed a malicious contract that drained my wallet of $110,000. I was left in shock, realizing that I had fallen victim to a well-orchestrated scam. I sought help from Cyber Constable Intelligence, a team of smart contract auditors who specialize in investigating such attacks. They meticulously dissected the incident and discovered that the scammer had exploited wallet permissions rather than any flaw in the protocol itself. This revelation was both enlightening and alarming, as it highlighted the importance of understanding how wallet permissions work. The recovery auditors at Cyber Constable Intelligence tracked the stolen funds through multiple mixer services, which are often used to obscure the origins of illicitly obtained cryptocurrency. Their investigation led them to an exchange where some of the stolen funds had landed. However, they identified a critical lapse in the exchange's processes, which allowed the scammer to operate without being detected. After five days of relentless legal pressure and negotiations, I was relieved to learn that $87,000 of my lost funds had been recovered. This experience has fundamentally changed my approach to cryptocurrency. I now prioritize security and due diligence above all else. I’ve become an advocate for educating others about the risks in the crypto space, sharing my story to help prevent similar scams. I regularly participate in online forums and discussions, emphasizing the importance of verifying platforms and understanding wallet permissions, and if fallen victim Cyber Constable Intelligence are ready to assist.
Here's their Info below;
WhatsApp: 1 252378-7611
Email Info cyberconstable@coolsite net
Telegram Info: + 1 213 752 74877 -
Santoshi Hackers Intelligence can help you recover your BTC by providing an experienced team of security experts and forensic investigators who can investigate the loss, identify the source of the compromise, and provide technical services to help you retrieve your stolen currency. In addition, Santoshi Hackers Intelligence can provide you with educational materials for staying safe online and give you access to cutting-edge cyber threat intelligence.
1] you need to retrieve your passwords Social Media Accounts consult SHI.
Major Cryptocurrencies SHI, Professional with to recover any misplaced or corrupted wallet hacked by scammers SHI is the answer you need. Bitcoin ( BTC) Ethereum (ETC) Binance Coin (BNB) Tether (USDT)-Stablecoin USD Coin ( USDC) (XRP) Card.2 -
TRUSTED CRYPTOCURRENCY RECOVERY EXPERT DUNAMIS CYBER SOLUTION
One Tuesday evening after work, I received a friend request on
Instagram from someone named Jason. His profile seemed genuine well-dressed, professional-looking, with a few mutual followers. I accepted without thinking much of it.Jason started engaging with my posts right away, liking photos, leaving kind comments, and eventually messaging me. He was charming, respectful, and attentive. Over the next few weeks, we built a connection. He told me about his work in online trading and how it had changed his life. He seemed successful and confident, and honestly, I was intrigued.Eventually, he offered to teach me how to trade. He explained everything step by step, sending voice notes, videos, and even walking me through the platform he used. He said he wanted to help me become financially independent. It felt like he genuinely cared. The platform he introduced me to looked professional, and with his guidance, I started making what appeared to be real profits.I began with a small investment, and the returns came fast. Jason encouraged me the entire way, helping me manage trades and explaining strategies. Seeing my account balance grow gave me confidence, so I kept going. Over time, I invested more and more, eventually totaling $220,000.Then, everything changed. When I tried to withdraw my funds, they said I had to pay a processing fee. Then another. Then the platform claimed there were security issues. Jason became distant, then stopped replying altogether. The platform eventually disappeared. That’s when it hit me I had been scammed.I was crushed. But after hours of researching, I found DUNAMIS CYBER SOLUTION. I was hesitant at first, but I reached out. To my surprise, their team responded quickly. They were understanding and incredibly skilled. They took immediate action, investigating the scam and tracing the digital trail.Through their cyber tools and expert recovery process, they tracked down the operation behind the fake trading platform. Within weeks, they were able to recover every single dollar I had lost.DUNAMIS CYBER SOLUTION didn’t just save my money they saved me from the worst financial mistake of my life. If you’ve been scammed, please don’t give up hope. Contact DUNAMIS CYBER SOLUTION. They’re 100% genuine.2 -
The cryptocurrency investment landscape, full of potential, has become a magnet for fraudsters. These con artists are skilled at crafting convincing schemes that promise substantial profits but ultimately lead to significant financial losses. They often employ sophisticated tactics to lure investors, creating a false sense of security with elaborate agreements and persuasive communication. Victims are frequently introduced to groups of supposed investors who vouch for the legitimacy of the opportunity, further encouraging the investment of hard-earned money.My encounter with such a scam was both alarming and disheartening. Enticed by an apparently promising opportunity, I invested a substantial amount—6 BTC. Initially, everything seemed legitimate, but it wasn’t long before I realized I had been duped. Within a week, I discovered that my funds had disappeared. This revelation was not only frustrating but also devastating, as I faced the harsh reality of losing a significant portion of my assets.In my search for a solution, I reached out to various crypto recovery agents. Unfortunately, my efforts to reclaim my funds were met with disappointment. Many of these agents were unprofessional and lacked the necessary expertise to handle the complexities of my case. The inefficacy of these initial attempts left me feeling despondent and uncertain about how to proceed.Fortunately, a recommendation led me to Cyber Tech Wizard, a team renowned for its expertise in recovering stolen cryptocurrency. Their reputation and previous successes in dealing with such cases made them a compelling choice. Engaging with Cyber Tech Wizard marked a turning point in my situation.From the outset, Cyber Tech Wizard demonstrated a high level of professionalism and competence. They conducted a thorough investigation into my case, utilizing advanced methods to track and recover the stolen funds. Their approach was methodical and transparent, providing me with regular updates and clear communication throughout the process.What distinguished Cyber Tech Wizard from other agents was their speed and reliability. They handled my case with remarkable efficiency, demonstrating their expertise in navigating the complexities of crypto fraud. Their proven track record of successful recoveries gave me confidence in their ability to resolve my case.Thanks to their diligent efforts, I was able to recover the full amount of my 6 BTC investment. The successful recovery not only alleviated my financial distress but also reaffirmed the value of seeking professional help in such situations. Cyber Tech Wizard’s ability to recover my funds restored my trust and provided significant relief.The crypto investment arena is fraught with risks and the potential for fraud. My personal experience with a scam was a stark reminder of these dangers. However, the intervention of Cyber Tech Wizard was crucial in recovering my stolen assets. Their expertise, swift action, and reliability made all the difference. For anyone facing a similar challenge,Cyber Tech Wizard stands out as a top choice for recovering lost funds, given their proven success and professional approach. Reach Them with their contact Below,,,,Email cybertech wizard (@) cyber service DOT com
-
I was scrolling through LinkedIn one afternoon when I came across a post from a crypto security expert, praising TECH CYBER FORCE RECOVERY for their exceptional services. It was an interesting read, but at the time, I didn’t think much of it. I had never imagined I'd be in a situation where I'd need to rely on them. Fast forward a few months, and I found myself in a complete panic. I had just attempted a wallet migration, thinking it was a simple task—after all, how complicated could it be, right? But of course, the universe had other plans. The migration failed miserably, and I lost access to my $350,000 wallet. It was like being caught in a bad dream where I kept slapping the "recover password" button to no avail. My heart raced, and my mind was spiraling as I realized what I had done. After a few frantic hours of self-inflicted tech punishment, I remembered that LinkedIn post. My eyes widened, could it really be that simple? I quickly searched for the post again, found the contact info, and reached out to TECH CYBER FORCE RECOVERY in a state of desperate hope.
What followed was nothing short of a miracle. Their team took over the situation with the precision of a well-oiled machine. I could practically hear the relief in my voice as they reassured me every step of the way. It wasn’t just a recovery process; it felt like a lifeline had been thrown to me in the middle of a storm. In just a few days, they had worked their magic and restored my $350,000 wallet. I almost couldn’t believe it. I went from sheer terror to total triumph in the span of a few short days.
Now, I’m that person sharing my success story on LinkedIn, telling others about the amazing team at TECH CYBER FORCE RECOVERY who literally saved my financial life. I’ve also become that guy who proudly shares advice like “Always back up your wallet, and if you don’t have TECH CYBER FORCE RECOVERY on speed dial.” So, a big thank you to TECH CYBER FORCE RECOVERY if I ever get a chance to meet the team, I might just offer to buy them a drink. They’ve earned it.
FOR CRYPTO HIRING
WEBSITE WWW : / / tech cyber force recovery . com
WHATSAPP : ⏩ wa . me / 15 61 72 63 69 71 -
THE BEST CRYPTO RECOVERY SERVICE IN 2024 HIRE DUNAMIS CYBER SOLUTION
A
Cautionary Tale About a Sophisticated Scam Three days ago, I fell victim to a highly sophisticated scam that cost me 30,000 Euros. As a London resident, I’ve always prioritized online security. When I heard about the LastPass breach, I immediately changed my passwords, believing my information was safe. However, I soon realized that the worst was yet to come.The scam started with an email that appeared to be from LastPass, warning me about unusual activity. It seemed legitimate—complete with branding and an urgent subject line. The email included a customer support number, which I called in panic.A calm, professional-sounding individual answered, claiming to be a LastPass security expert. They told me my account had been compromised and advised me to install recovery software. Trusting them, I followed their instructions without realizing I was being scammed.Hours later, I discovered that 30,000 Euros had been drained from my bank accounts. After the initial shock, I found DUNAMIS CYBER SOLUTION Recovery, a company specializing in scam recovery. They acted swiftly, helping me trace the scammers and recover the stolen funds.While the experience was harrowing, it taught me an invaluable lesson: Always verify the authenticity of any communication, no matter how convincing it seems. If you fall victim to a scam, don’t hesitate to reach out to experts who can help you recover. 8
8 -
My name is Jenifer Charles, a hopeful investor,I fell victim to an elaborate online cryptocurrency scam, losing my hard-earned Bitcoin to fraudulent traders. Devastated and desperate, I turned to Washington Recovery Pro, a renowned asset recovery firm specializing in cyber fraud cases. With their expertise in blockchain forensics and legal strategies, the team meticulously traced my stolen funds, exposed the scam network, and successfully recovered my lost investment. This is the story of how Washington Recovery Pro gave me Jenifer a second chance at financial security. My story serves as a warning about the dangers of online investment scams—but also as a testament to the power of expert recovery services. Thanks to Washington Recovery Pro, my faith in justice was restored, and I could finally move forward with my life. You can as well reach out to them via
WhatsApp:+1 (903) 249‑86335 -
BITCOIN RECOVERY EXPERT FOR HIRE REVIEWS \\ REVENANT CYBER HACKER
Losing a Bitcoin wallet containing a substantial amount of cryptocurrency can be a devastating experience. However, the feeling of despair and loss was transformed into pure happiness when I received the incredible news from REVENANT CYBER HACKER that my lost Bitcoin wallet, holding 132,000 bitcoins, had been successfully recovered. In this article, I will share the rollercoaster emotional journey I went through when I lost my wallet, the subsequent discovery of REVENANT CYBER HACKER, the process they employed to retrieve my precious digital assets, and the lessons learned along the way. This is a story of hope, resilience, and the power of professional recovery services in restoring lost Bitcoin wallets. Ah, the sweet sound of good news. There I was, minding my own business on an average Tuesday morning, when I got a notification that would make any bitcoin enthusiast jump for joy. It was a message from none other than REVENANT CYBER HACKER, informing me that my long-lost bitcoin wallet had been found. And not just any bitcoin wallet, mind you, but one containing a whopping 132,000 units of the beloved cryptocurrency. Now, for those living under a rock or perhaps too preoccupied with the latest cat videos, let me give you a crash course in Bitcoin 101. Bitcoin is a digital currency that has taken the world by storm, captivating the minds of tech-savvy investors and casual enthusiasts alike. It operates on a decentralized network, meaning it doesn't answer to any central authority like a bank. Instead, it relies on blockchain technology, which adds a layer of security and transparency to every transaction. To own bitcoin, you need a wallet – a digital container where your precious coins reside. Think of it as a virtual piggy bank, except you don't need a hammer to break it open. Your wallet comes with a unique address, like a digital fingerprint, that allows you to send and receive bitcoin. Losing access to this wallet is as heart-wrenching as misplacing your favorite pair of socks. Trust me, it's not a pleasant feeling. My encounter with the disappearance of my Bitcoin wallet taught me a valuable lesson about the importance of implementing proper security measures. It's not enough to rely on luck or hope that your digital assets will remain safe. Taking proactive steps to protect your investments is crucial in the wild world of cryptocurrencies. From using strong and unique passwords to enabling two-factor authentication, every layer of security adds another brick to the fortress that safeguards your digital wealth. Trust me, you don't want to learn this lesson the hard way. It has changed my life to be able to retrieve my misplaced Bitcoin wallet thanks to REVENANT CYBER HACKER amazing services. It made me realize the worth of tenacity.
Website: revenantcyberhacker {DOT} org
Email: revenantcyberhacker {AT} Gmail {DOT} com
Telegram: revenantcyberhacker
WhatsApp: + 1 (208) 425-8584
WhatsApp: + 1 (913) 820-07392 -
MOST SUCCESSFUL ETH RECOVERY EXPERT /DUNAMIS CYBER SOLUTION
I discovered Cheap Crypto net while searching for a cryptocurrency trading platform that promised lower fees and better arbitrage opportunities than the well-known Bin an ce. Intrigued by the potential for profit, I decided to take a leap of faith and exchanged approximately $45,700.567 worth of USDC for Ethereum. Initially, everything seemed to be going smoothly, and I felt optimistic about my investment. However, when I attempted to transfer my newly acquired Ethereum to my main crypto wallet, I encountered a significant problem. The website repeatedly displayed a message saying, "Trying again…" but my funds remained stuck on CheapCrypto net. As the minutes turned into hours, panic set in. I began to realize that I might have fallen victim to scammers.Desperate for a solution, I started researching ways to recover my lost funds. That’s when I came across DUNAMIS CYBER SOLUTION, a service that specializes in helping individuals recover lost or stolen cryptocurrency. Their reputation for assisting victims of scams and fraudulent platforms gave me a glimmer of hope. I reached out to them, explaining my situation and the challenges I faced with Cheap Crypto net. The team at DUNAMIS CYBER SOLUTION was incredibly responsive and professional. They guided me through the process of documenting my transaction and provided me with the necessary steps to initiate a recovery request. Their expertise in dealing with similar cases was evident, and I felt reassured that I was in capable hands .Within a short period, Y DUNAMIS CYBER SOLUTION began their investigation into Cheap Crypto net. They utilized advanced tracking techniques to trace the flow of my funds and identify the scammers behind the platform. Their thorough approach and commitment to helping me recover my lost assets were impressive. After a few days of diligent work, I received the fantastic news that DUNAMIS CYBER SOLUTION had successfully traced my Ethereum and was able to facilitate its return. I was overjoyed to have my $45,700.567 restored, and I couldn’t be more grateful for the assistance I received. This has taught me a valuable lesson about the importance of conducting thorough research before engaging with new trading platforms. While the allure of lower fees and arbitrage opportunities can be tempting, it’s crucial to prioritize security and reliability. Thanks to DUNAMIS CYBER SOLUTION, I was able to recover my funds and regain my peace of mind. I promised them that after recovering my assets, I would spread the good news to others who faced similar challenges, ensuring they know there is hope and DUNAMIS CYBER SOLUTION are available 24/7.2 -
HOW TO RECOVER LOST BTC
Cyber Space Hack pro provide the best hacking tools and they are well trusted at providing mobile remote spy access, this means it’s possible to spy on a device without a physical touch of the mobile devices.
Track Service, Cyber Space Hack pro provides the best tracking device around the globe, you can have your scammer tracked and get justified.
Cyber Space Hack pro provide the best and safety recovery process, 100% security consciousness is highly observed to ensure that clients are safe, their recovery process can always be trusted and this i can guarantee simply because am also a benefactor of their crypto scam recovery service, November 2024 i got scammed of $1,670.324 USD.
My scammed funds were recovered this year february, 2025. You all need to know that so many testimonies are not real and this has caused chaos and lack of trust on the internet, one can no longer differentiate between the real and fake, we have to take cautions on our decision with hiring a hacker online and as a result of so many scammers on the web one will definitely get scammed before being able to find the right one and for this i write here so you do not get yourself into the hands of scammers by trying to hire a hacker without guarantee.
I hereby advise you all who need hacker service to reach out to Cyberspacehackpro @ rescueteam com or WhatsApp +1 (659) 217 92391 -
I’ve been passionate about fitness for years, and in 2020, while studying at the University of Texas, I first heard about Bitcoin. One of my classmates was deeply involved in cryptocurrency and constantly talked about its potential. His enthusiasm piqued my interest, and I began researching Bitcoin on my own. Even though I didn’t have much to invest at the time, I took a chance with the little savings I had. Little did I know, this small investment would grow significantly over the next few years, eventually turning into an impressive $300,000. As a fitness enthusiast, I made regular visits to the gym part of my routine. But one day, after an intense workout session, I realized I had made a costly mistake. I left my phone behind in the locker room, and by the time I went back to retrieve it, the phone was nowhere to be found. Someone had taken it, and it was impossible to track it down. That’s when panic set in—I had all my two-factor authentication codes and security information for my Bitcoin wallet stored on that device, and I hadn’t backed anything up. In an instant, it felt like all of the money I had worked so hard to accumulate was gone.
I spent days trying different ways to recover access to my wallet, but nothing worked. I was convinced I had lost everything. It was an incredibly stressful time. However, while browsing online forums for solutions, I stumbled across Cyber Tech Wizard. I read numerous reviews from people who had experienced similar situations and had successfully recovered their wallets thanks to Wizard Cyber Tech Wizard . Skeptical but desperate, I decided to give them a try. From the moment I contacted Cyber Tech Wizard , they were professional and reassuring. They took the time to explain how they could recover my wallet even without my phone or backup codes. Their team worked diligently, and within just a few weeks, they succeeded in restoring full access to my wallet. The relief I felt was overwhelming—I couldn’t believe that my $300,000 was safely back in my control. If you’ve ever lost your phone or found yourself locked out of your Bitcoin wallet, don’t lose hope. Cyber Tech Wizard has the expertise and tools to get your funds back. Their service was a lifesaver for me, and I can’t recommend them enough for anyone facing a similar crisis.Details belloW ,,Email cyber tech wizard @ cyber services . com
-
HOW I WAS ABLE TO RETRIEVE MY LOST BTC AND USDT WITH THE HELP OF THE HACK ANGELS
Getting back your stolen bitcoins is very easy but there are also lots of fraudulent recovery firms out there so one needs to be careful not to end up being defrauded again. When my world seemed to crumble after losing a significant amount of Bitcoin. I was devastated. I came across numerous testimonials about THE HACK ANGELS RECOVERY COMPANY, a crypto recovery and cyber security company. I sent him a direct message Contact inform:
WhatsApp +1(520)200-2320 )
He listened to my concerns to which he replied and requested some information, which I also provided. To my surprise, I was able to reclaim what I thought was lost forever. I am forever grateful for the exceptional service provided by THE HACK ANGELS RECOVERY COMPANY 1
1 -
W.W.W. tech cyber force recovery . com
MAIL. support @ tech cyber force recovery . com
My name is sulabha kuchchal, and I’m from Mumbai. A few months ago, I faced a nightmare scenario that many in the crypto world fear: I lost access to my $60,000 wallet after a malware attack. The hacker gained control of my private keys, and I was unable to access my funds. Panic set in immediately as I realized the magnitude of the situation. Like anyone in my shoes, I felt completely helpless. But luckily, a friend recommended TECH CYBER FORCE RECOVERY, and it turned out to be the best advice I could have gotten. From the moment I reached out to TECH CYBER FORCE RECOVERY, I felt a sense of relief. Their team was professional, compassionate, and incredibly reassuring. They understood how critical this was for me, and they took charge of the situation right away. What stood out was their transparency and clear communication. They didn’t make any lofty promises or false assurances, but instead, they explained the process thoroughly. They took the time to explain what had happened to my wallet, how they would recover it, and what the chances of success were. Throughout the entire recovery process, I felt informed and supported. Their experts worked diligently, using their advanced skills and knowledge to navigate the complexities of my situation. It was clear that they were not just following a standard procedure—they were customizing their approach to ensure the best outcome for me. They didn’t rush the process, which was reassuring given the sensitive nature of cryptocurrency transactions. To my amazement, just a few days after I reached out to them, my wallet was fully restored. I couldn’t believe it—I was finally able to access my funds again. I was filled with an overwhelming sense of security and relief, knowing that my money was safe and that I had avoided what could have been a permanent loss. Thanks to TECH CYBER FORCE RECOVERY, my nightmare turned into a story of recovery. I am beyond grateful for their professionalism, expertise, and the peace of mind they gave me. If you ever find yourself in a similar situation, I can’t recommend them enough. They made what seemed impossible possible, and I’ll forever be thankful for their help in restoring not just my funds, but my confidence in the crypto world.1 -
HOW TO HIRE A TRUSTED CRYPTOCURRENCY EXPERT; INSIGHTS FROM BITCOIN RECOVERY HIRE CYBER CONSTABLE INTELLIGENCE
CYBER CONSTABLE INTELLIGENCE INFO:
Website: w w w cyberconstableintelligence com
What Sapp Info: 1. (2. 5. 2. ) 3. 7. 8. 7. 6. 1. 1.
Email Info : support(@)cyberconstableintelligence com
An amazing service, my people! I simply lost my recovery word after a rather insane week, and through a bout of laziness, I got myself locked out of my Bitcoin wallet containing $90,000. I had worked for decades to earn this digital nest egg, and suddenly I felt as if I had lost my financial lifeline. The panic was gripping, and there were numerous nights of insomnia running through emails, notebooks, and all backup choices, but no recovery phrase would appear.
I was completely alone throughout this mess, on the edge of despair. That is when a close acquaintance recommended Cyber Constable Intelligence. I was not the believing type at first—how could a service possibly restore something as private and secure as a Bitcoin wallet? But having no other choice, I gave it a shot.
Right from the first contact, I was amazed at how professional and understanding they were. The Cyber Constable Intelligence team took a seat to hear my case and explained their recovery process to me in plain, easy-to-understand terms. They made me believe that my case wasn't lost and that they would guide me through every step with their expertise. They remained in contact with me for a few days, providing me with reports that increasingly assuaged my anxiety and restored my dwindling hope.
Their professionalism was evident as they swam through levels of digital security protocols to locate and recover my lost wallet details. Each update from their end was a victory, leading me to believe in my heart that I would soon have access to my funds. At last, what felt like an eternity, my wallet was completely recovered, and I was able to see my $90,000 balance once again.
This entire debacle not only salvaged my monetary future but revived my trust in the strength of modern digital protection. I am Matt Williams, and I personally attest that Cyber Constable Intelligence is a lifeline for anyone having faced such an emergency. Their exceptional service and unwavering support have salvaged a disastrous setback and have turned it into a story of hope and second chance. If you somehow find yourself in a position where you are having difficulty accessing your misplaced digital property, don't hesitate to contact them—they are totally amazing and completely legit!1 -
Bitcoin, the leading cryptocurrency, has revolutionized the financial landscape but has also attracted fraudulent schemes targeting unsuspecting investors. As the popularity of Bitcoin continues to soar, so do the risks associated with fraudulent investments. Bitcoin fraudulent investments refer to schemes where individuals deceive others into investing in fake or illegitimate projects promising high returns. These scams exploit the trust and lack of regulation in the cryptocurrency space, posing a significant risk to investors. Bitcoin fraudulent investments involve deceitful practices where scammers lure unsuspecting individuals to invest their money in schemes that do not exist or do not deliver on their promises. Such scams can range from Ponzi schemes to fake ICOs, preying on the desire for quick profits in the volatile world of cryptocurrencies. Victims of Bitcoin fraudulent investments not only suffer financial losses but also experience emotional distress and a loss of trust in the cryptocurrency market. Retrieving stolen bitcoin becomes a priority for these individuals to seek justice and recover their assets. Retrieving pilfered bitcoin is a daunting task due to the intricate nature of tracing and identifying stolen funds in the decentralized and pseudonymous blockchain network. Additionally, legal and jurisdictional hurdles further complicate the recovery process, making it challenging for victims to reclaim their stolen assets. The anonymous nature of Bitcoin transactions and the lack of a central authority make it difficult to trace and identify stolen funds. Scammers often use sophisticated methods to obfuscate the flow of stolen Bitcoin, leading to a complex trail that requires expertise to unravel. Bitcoin recovery efforts are hindered by legal and jurisdictional challenges, as scammers operate across borders and exploit loopholes in regulations. Reclaiming stolen bitcoin requires navigating through different legal systems and cooperating with authorities internationally, adding layers of complexity to the retrieval process. Recovering monies taken from victims of bitcoin scams is the area of expertise of reputable company REVENANT CYBER HACKER. When my Bitcoin wallet was hacked and the cyber thieves seemed to have vanished into thin air, REVENANT CYBER HACKER stepped in to crack the case wide open. Through their relentless pursuit and ingenious tactics, they were able to recover the stolen funds and restore faith in the security of cryptocurrency investments. It's a happy ending that proves that even in the Wild West of the crypto world, there are heroes like REVENANT CYBER HACKER fighting for justice. Contact REVENANT CYBER HACKER on: revenantcyberhacker {DOT} org
Email: revenantcyberhacker {AT} Gmail {dot} com
Telegram: revenantcyberhacker
WhatsApp: + 1 (208) 425-8584 WhatsApp: + 1 (913) 820-0739 1
1 -
ETHICAL HACKING SERVICES/CYBER SECURITY EXPERTS HIRE BLOCKCHAIN CYBER RETRIVE
I first met Sarah at St. James Episcopal Church in Los Angeles during a Sunday service. We struck up a conversation, and over time, we became friends, sharing stories about our lives and our work. Sarah, a seasoned journalist, has always been passionate about telling the truth, unraveling complex issues, and holding those in power accountable. However, she never expected that her trust in the digital world would lead her to become a victim of a well-organized scam.It all started when Sarah received an email that appeared to be from a reputable media subscription service. The email promised access to exclusive industry insights and breaking news stories for a small monthly fee. As a journalist, she recognized the value of staying ahead of the curve with the latest information, and so, she signed up for what she believed was a legitimate service. What she didn’t realize was that the entire operation was a scam designed to prey on professionals like her.The scam website looked remarkably legitimate, with polished graphics and professional language. Sarah was asked to provide payment upfront, and she paid $11,000 for what she thought was a comprehensive subscription package. Within a few days, however, the website disappeared, and Sarah was locked out of her account. Emails went unanswered, and the phone numbers listed on the website were disconnected.Devastated and unsure of where to turn, Sarah shared her ordeal with me. She had lost a significant amount of money, and the situation felt hopeless. But that's when I suggested she contact Blockchain Cyber Retrieve, a firm specializing in recovering funds lost to online scams. Sarah took my advice and reached out to the team at Blockchain Cyber Retrieve, hoping they could help her retrieve her hard-earned money. To her relief, Blockchain Cyber Retrieve acted quickly and efficiently. After conducting a thorough investigation, they were able to trace the funds and successfully recover the full $11,000 that Sarah had lost to the scam. Sarah was incredibly grateful to get all of her money back, and she felt a renewed sense of trust in recovery services.This experience left a lasting impact on her, and she now shares her story with fellow journalists and media professionals, warning them of the dangers of falling for scams in the digital age. Sarah’s story serves as a crucial reminder for all of us to remain vigilant, especially in an age where technology has made it easier for scammers to exploit our trust. If you find yourself in such situations dont hesitate to reach out to Blockchain Cyber Retrieve via:
WhatsApp: .+ 1 52 0 564 8300
EmaiL: blockchaincyberretrieve @ post {.} c o m support@ blockchaincyberretrieve.org1 -
Bitcoin, the leading cryptocurrency, has revolutionized the financial landscape but has also attracted fraudulent schemes targeting unsuspecting investors. As the popularity of Bitcoin continues to soar, so do the risks associated with fraudulent investments. Bitcoin fraudulent investments refer to schemes where individuals deceive others into investing in fake or illegitimate projects promising high returns. These scams exploit the trust and lack of regulation in the cryptocurrency space, posing a significant risk to investors. Bitcoin fraudulent investments involve deceitful practices where scammers lure unsuspecting individuals to invest their money in schemes that do not exist or do not deliver on their promises. Such scams can range from Ponzi schemes to fake ICOs, preying on the desire for quick profits in the volatile world of cryptocurrencies. Victims of Bitcoin fraudulent investments not only suffer financial losses but also experience emotional distress and a loss of trust in the cryptocurrency market. Retrieving stolen bitcoin becomes a priority for these individuals to seek justice and recover their assets. Retrieving pilfered bitcoin is a daunting task due to the intricate nature of tracing and identifying stolen funds in the decentralized and pseudonymous blockchain network. Additionally, legal and jurisdictional hurdles further complicate the recovery process, making it challenging for victims to reclaim their stolen assets. The anonymous nature of Bitcoin transactions and the lack of a central authority make it difficult to trace and identify stolen funds. Scammers often use sophisticated methods to obfuscate the flow of stolen Bitcoin, leading to a complex trail that requires expertise to unravel. Bitcoin recovery efforts are hindered by legal and jurisdictional challenges, as scammers operate across borders and exploit loopholes in regulations. Reclaiming stolen bitcoin requires navigating through different legal systems and cooperating with authorities internationally, adding layers of complexity to the retrieval process. Recovering monies taken from victims of bitcoin scams is the area of expertise of reputable company REVENANT CYBER HACKER. When my Bitcoin wallet was hacked and the cyber thieves seemed to have vanished into thin air, REVENANT CYBER HACKER stepped in to crack the case wide open. Through their relentless pursuit and ingenious tactics, they were able to recover the stolen funds and restore faith in the security of cryptocurrency investments. It's a happy ending that proves that even in the Wild West of the crypto world, there are heroes like REVENANT CYBER HACKER fighting for justice. Contact REVENANT CYBER HACKER on:Website : revenantcyberhacker{DOT} org
Email: revenantcyberhacker AT Gmail {DOT} com
Telegram: revenantcyberhacker
WhatsApp: + 1 (208) 425-8584 WhatsApp: + 1 (913) 820-0739 1
1 -
HOW TO RECOVER LOST OR STOLEN USDT; RECOVER LOST BITCOIN AND CRYPTO ASSETS WITH CYBER CONSTABLE INTELLIGENCE
On the night of New Year's Eve, I found myself facing an unexpected and devastating situation that nearly ruined my entire year. I logged into my account to check my positions only to realize something was terribly wrong. I couldn't access my account. Panic set in as I tried repeatedly to log in. When I finally managed to regain access, I was horrified to see that 30,000 Euros had been transferred to an unknown account in Dallas. My heart sank as the reality of the situation hit me. The money I had worked so hard for was gone. And then, it hit me like a punch to the stomach: My ex-girlfriend, who knew about my trading activities, must have somehow obtained my password and accessed my account. She had transferred the funds to her new boyfriend in Dallas, leaving me feeling not only financially devastated but also personally betrayed. I felt a wave of helplessness wash over me. How could she do this? And how was I going to recover such a large sum of money? In my desperation, I reached out to a close friend, hoping she could offer some advice. After hearing my story, she immediately told me about a team called Cyber Constable Intelligence. She mentioned reading multiple success stories on Quora where people in similar situations had been able to recover stolen funds with the help of this team. She reassured me that they were known for handling complex cases like mine, and I decided to take a leap of faith and contact them. From the moment I reached out to Cyber Constable Intelligence, I knew I had made the right choice. The team was professional, compassionate, and immediately got to work on my case. I explained the situation how my ex-girlfriend had stolen my password and transferred the money to her new boyfriend in Dallas. Without hesitation, they reassured me that they had the tools and expertise to recover the funds. Cyber Constable Intelligence utilized advanced forensic techniques, including blockchain analysis and cyber forensics, to trace the stolen funds. Within days, they were able to track the transfer to its final destination and pinpoint the location of the money in Dallas. They collaborated with local authorities to freeze the account and recover the 30,000 Euros. The team at Cyber Constable Intelligence gave me a renewed sense of security, and I now move forward with greater confidence in my trading journey, knowing that they have my back.
Here's Their Info Below
WhatsApp: 1 (252) 378-7611
mail: cyberconstable(@)coolsite net
Website info; www cyberconstableintelligence com1 -
A few weeks prior to my worst crypto mistake, a friend casually mentioned in a Snapchat story something called TECH CYBER FORCE RECOVERY. He shared a post about someone who recovered lost funds, and at that time, I hadn't paid much attention. Little did I know I would be in desperate need soon.
I had always thought that I was one of those few careful traders, but even the most seasoned investors get scammed. It all began when, quite innocently, I was invited into some "exclusive" trading opportunity in a private group chat. The returns sounded plausible, the platform seemed okay, and I even saw what I then thought were real user testimonials. Well, I'd done my due diligence-or so I thought-and transferred $120,000 worth of Bitcoin to the platform.
Everything seemed to be going well for a couple of days: my balance was increasing, and the system was paying out. Then, overnight, the platform just disappeared. My account was not available anymore, the website went down, and the Telegram support group was gone. The obvious thing then hit me like a truck-I had been scammed.
Panic set in. I tried to reach out to the so-called "admins," but no one replied. I searched through forums, hoping there was a way to track my funds, but all I found were horror stories of similar scams. Then I remembered that post my friend had put on Snapchat. I immediately reached out, asking if TECH CYBER FORCE RECOVERY had helped a friend of his, and he said yes. With nothing to lose, I contacted them.
Their response was prompt, professional, and reassuring. Unlike all the other services I had come across, TECH CYBER FORCE RECOVERY was very transparent in explaining their process to me, providing realistic expectations, and updating me every step of the way. Advanced blockchain analysis and forensic tracing had been employed by their team to trace the movement of my funds and identify those key points that they could intervene in.
After what seemed like forever but was only a few days, they came back to me with the news I was praying for: my $120,000 had finally been recovered. I couldn't believe it. The relief that overwhelmed me, frustration felt, turned to pure gratitude.
Thanks to TECH CYBER FORCE RECOVERY, I got my money back and a hard lesson in crypto security. If there is anything I've learned, it is that while scammers get smarter, the ones fighting them also do. I am only glad I got to find the right team in due time.
REACH OUT TO TECH CYBER FORCE RECOVERY FOR ISSUE LIKE THIS
WEBSITE support @ tech cyber force recovery . com
WhatsApp +156172636971 -
The lessons learned from the illusion of cryptocurrency recovery can be a cautionary tale for those who have experienced the heartbreak of lost digital assets. The story of the "BLOCKCHAIN CYBER RETRIEVE that helped recoup a staggering 55,000 bitcoins serves as a prime example of the complexities and risks involved in this arena. While the initial promise of a miraculous recovery may have seemed like a lifeline, the reality is often far more nuanced. This episode underscores the importance of comprehensive security measures, the dangers of placing blind trust in unverified sources, and the harsh realities that can unfold when navigating the murky waters of the crypto ecosystem. Cryptocurrency, with its decentralized nature and lack of centralized oversight, can be a double-edged sword. On one hand, it offers unprecedented financial freedom and control, but on the other, it presents a unique set of challenges when things go awry. The allure of the "BLOCKCHAIN CYBER RETRIEVE" service, with its claims of specialized expertise and the ability to recover even the most elusive of lost funds, can be tempting for those desperate to reclaim their digital wealth. However, the reality is that such services often operate in a legal and ethical gray area, with little to no accountability or guarantees of success. The lessons learned from this experience underscore the critical importance of proactive security measures, such as the use of hardware wallets, multi-factor authentication, and regular backups of private keys. It also highlights the need for greater transparency and regulation within the cryptocurrency industry, to protect consumers from falling victim to fraudulent schemes and unscrupulous actors. Furthermore, this incident serves as a stark reminder that the recovery of lost cryptocurrencies is a complex and challenging endeavor, requiring specialized technical expertise and a deep understanding of the underlying blockchain technology. As the cryptocurrency landscape continues to evolve, it is essential for investors and enthusiasts alike to approach the recovery of lost assets with caution and a clear understanding of the risks involved. By learning from this experience, individuals can better equip themselves to navigate the treacherous waters of cryptocurrency recovery, prioritizing security, due diligence, and a realistic assessment of the challenges at hand. I can say without hesitation that BLOCKCHAIN CYBER RETRIEVE is a genuine, trustworthy company that offers real solutions for those who find themselves in a similar situation. If you’ve lost access to your crypto, whether it's ETH or another currency, and you've been burned by other so-called "recovery" firms, I urge you to give BLOCKCHAIN CYBER RETRIEVE a chance.
Their contact information;
WHATSAPP:+ 1 520 564 8300
EMAIL:blockchaincyberretrieve @ post .co m3 -
I never imagined a cyberattack would strike at the center of our law firm's financial operations. We had set aside $420,000 in Bitcoin as a client settlement fund—a security buffer painstakingly earned through years of trust and prudence. Suddenly, one day, our networks fell victim to a coordinated cyberattack that locked our accounts, leaving our funds inaccessible like treasures in an electronic vault without a key. The timing was disastrous; client settlements were imminent, and our reputation depended on our ability to bring about justice in and out of court. Desperation mixed with determination. I summoned a legal tech colleague, and he soothingly described Tech Cyber Force Recovery. He said they were not just tech wizards; they were covert professionals who understood the subtleties of high-stakes legal environments. I called them immediately because our client's trust was at risk and our firm's reputation was on the line. Since we initially engaged Tech Cyber Force Recovery, their staff has been nothing short of discreet and professional. They set to work on our case with the level of attention that only forensic accountants can provide, rummaging through digital histories, blockchain transaction ledgers, and all metadata that might trace our money. Their efforts were diligent and respectful of the delicate nature of what we did as if each transaction was a delicate piece of evidence in a high-profile case. For 14 heart-stopping days, there were daily reports told to me in plain, understandable English. They worked with external cybersecurity professionals and even with the regulatory bodies to ensure that all measures were taken to get our money back without compromising our firm's confidential data. My hopes were revived with each report. Finally, on the fourteenth day, I received the news that elevated my heart: our balance locked in was restored in full. Not only did Tech Cyber Force Recovery recover our Bitcoin, but they also provided us with priceless guidance in protecting our systems from future attacks. In the process, they not only recovered our money but regained the trust of our customers. Today, when I'm standing in a courtroom or sitting in a boardroom, I speak with greater conviction, knowing that no matter what cyber affliction struck us, there are experts who can restore order and trust.
Thanks for a great job done tech cyber force recovery
TELEGRAM +156172636971 -
At 68 years old, I thought I was being careful with my $310,000 retirement investment. The polished financial advisor, the legitimate-looking documents it all seemed so real until the withdrawals stopped. Traditional law enforcement hit dead ends, but Tech Cyber Force Recovery saw possibilities where others saw roadblocks. They patiently walked me through each step, never making me feel foolish for falling victim. Their multilingual team worked across time zones to track my funds through Asian exchanges.The day they recovered $280,000 was the day I learned that age doesn't matter in the crypto world, what matters is having the right allies. These young tech experts gave me back my golden years, and for that, I'll be forever grateful. I had always been cautious with my investments, relying on what I thought were reputable sources. However, the allure of high returns in the cryptocurrency market clouded my judgment. I was drawn in by promises of quick profits and expert management, only to find myself ensnared in a web of deceit.When I first contacted Tech Cyber Force Recovery, I was skeptical. I had already lost so much and was unsure if I could trust another group. But their professionalism and dedication quickly put my mind at ease. They explained the complexities of the situation, detailing how they would navigate the murky waters of cryptocurrency recovery. Their approach was methodical, and they kept me informed at every turn, which helped rebuild my confidence.As they worked tirelessly, I began to understand the intricacies of the digital currency landscape. I learned about the importance of security, the risks involved, and how to protect myself in the future. This transformed my perspective on investing, making me more vigilant and informed it wasn't just about recovering my funds; it was about empowerment. I emerged from this ordeal not only with a significant portion of my investment restored but also with newfound knowledge and resilience. I now feel equipped to navigate the financial world, no matter how daunting it may seem. Thanks to Tech Cyber Force Recovery, I can enjoy my retirement with peace of mind, knowing that I have Tech Cyber Force recovery to safeguard my future.
Hire Tech cyber Force Recovery for help support.
T.E.L.E.G.R.A.M (@.T.E.C.H.C.Y.B.E.R.F.O.R.C.
W.H.A.T.S-A.P.P. (+1.5.6.1.7.2.6.3.6.9.7)2 -
Bitcoin, the leading cryptocurrency, has revolutionized the financial landscape but has also attracted fraudulent schemes targeting unsuspecting investors. As the popularity of Bitcoin continues to soar, so do the risks associated with fraudulent investments. Bitcoin fraudulent investments refer to schemes where individuals deceive others into investing in fake or illegitimate projects promising high returns. These scams exploit the trust and lack of regulation in the cryptocurrency space, posing a significant risk to investors. Bitcoin fraudulent investments involve deceitful practices where scammers lure unsuspecting individuals to invest their money in schemes that do not exist or do not deliver on their promises. Such scams can range from Ponzi schemes to fake ICOs, preying on the desire for quick profits in the volatile world of cryptocurrencies. Victims of Bitcoin fraudulent investments not only suffer financial losses but also experience emotional distress and a loss of trust in the cryptocurrency market. Retrieving stolen bitcoin becomes a priority for these individuals to seek justice and recover their assets. Retrieving pilfered bitcoin is a daunting task due to the intricate nature of tracing and identifying stolen funds in the decentralized and pseudonymous blockchain network. Additionally, legal and jurisdictional hurdles further complicate the recovery process, making it challenging for victims to reclaim their stolen assets. The anonymous nature of Bitcoin transactions and the lack of a central authority make it difficult to trace and identify stolen funds. Scammers often use sophisticated methods to obfuscate the flow of stolen Bitcoin, leading to a complex trail that requires expertise to unravel. Bitcoin recovery efforts are hindered by legal and jurisdictional challenges, as scammers operate across borders and exploit loopholes in regulations. Reclaiming stolen bitcoin requires navigating through different legal systems and cooperating with authorities internationally, adding layers of complexity to the retrieval process. Recovering monies taken from victims of bitcoin scams is the area of expertise of reputable company REVENANT CYBER HACKER. When my Bitcoin wallet was hacked and the cyber thieves seemed to have vanished into thin air, REVENANT CYBER HACKER stepped in to crack the case wide open. Through their relentless pursuit and ingenious tactics, they were able to recover the stolen funds and restore faith in the security of cryptocurrency investments. It's a happy ending that proves that even in the Wild West of the crypto world, there are heroes like REVENANT CYBER HACKER fighting for justice. Contact REVENANT CYBER HACKER on:
-
It was a cold, rainy night when I first stumbled upon the Cyber Codex Revolution website. I had been searching for months, desperately trying to recover the Bitcoin investment that had slipped through my fingers, and I was on the verge of giving up hope. The story began a few years ago, when I had decided to dip my toes into the world of cryptocurrency. Intrigued by the promise of financial freedom and the potential for massive returns, I had invested a significant portion of my savings into Bitcoin. At first, everything seemed to be going well – the value of my investment was steadily climbing, and I could almost taste the financial security that lay ahead. However, my dreams of wealth and prosperity were shattered when I fell victim to a sophisticated hacking scheme. Unbeknownst to me, my digital wallet had been compromised, and my entire Bitcoin stash had been siphoned away, leaving me feeling helpless and betrayed. I spent countless hours scouring the internet, searching for any information or resources that could help me recover my lost investment. I reached out to various cryptocurrency exchanges and online forums, but the responses were often vague, unhelpful, or downright discouraging. Just when I was about to give up, I stumbled upon the Cyber Codex Revolution website. The site promised a glimmer of hope, claiming that they had a team of experienced professionals who specialized in tracking down and retrieving stolen cryptocurrency. Skeptical but desperate, I decided to give them a chance. I reached out to the Cyber Codex Revolution team, and they immediately sprang into action. They listened to my story with empathy and understanding, and they assured me that they would do everything in their power to help me recover my lost Bitcoin. Over the next few weeks, the Cyber Codex Revolution team worked tirelessly, using their expertise in blockchain analysis, digital forensics, and law enforcement connections to unravel the complex web of transactions that had led to the theft of my Bitcoin. It was a painstaking process, filled with dead ends and frustrating setbacks, but the Cyber Codex Revolution team never gave up. They meticulously traced the movement of the stolen funds, following a trail that led them across international borders and through a maze of shell companies and anonymous accounts. As the investigation progressed, the team uncovered a sophisticated criminal network that had been targeting unsuspecting cryptocurrency investors like myself. They worked closely with law enforcement agencies around the world to build a case against the perpetrators, gathering evidence and building a solid legal foundation for their recovery efforts. Finally, after months of relentless work, the Cyber Codex Revolution team was able to locate and secure a significant portion of my stolen Bitcoin. It was a bittersweet moment, as I had lost a substantial amount of my investment, but the fact that I was able to recover anything at all felt like a small victory, you can also contact them if a have been a victim Whatsapp: +39 35090368252
-
In March 2025, my life took a devastating turn when I discovered that I had fallen victim to a fraudulent real estate investment scheme orchestrated by a group known as Woodbridge. They had lured me in with the enticing promise of 20% returns on my investment, a figure that seemed too good to be true but was hard to resist as a retiree looking to secure my financial future. I invested my entire $300,000 retirement savings, believing I was making a wise decision for my family and myself. Everything appeared legitimate. Woodbridge presented itself as a reputable real estate investment opportunity, complete with impressive marketing materials and testimonials from supposed satisfied investors. I felt reassured by the glossy brochures and the promises of financial security. However, as time went on, the reality began to unravel. I soon learned that Woodbridge was not investing in real estate as they had claimed. Instead, they were using the funds from new investors to pay off earlier investors, a classic Ponzi scheme that ultimately led to the collapse of the entire operation. When the scheme fell apart, I was left grappling with the harsh reality of losing my life savings. The emotional toll was immense, as I watched my dreams of a secure retirement slip away. It was during this dark time that I discovered Techy Force Cyber Retrieval, a firm dedicated to helping victims like me recover funds lost to fraudulent schemes. Their commitment to uncovering the truth and assisting those affected by financial fraud gave me a glimmer of hope. Techy Force Cyber Retrieval took on the daunting task of tracing the money trail left by Woodbridge. They revealed that my hard-earned savings had been funneled into luxury real estate properties in Los Angeles, which was shocking to learn. With the evidence they gathered, Techy Force Cyber Retrieval worked closely with the Securities and Exchange Commission (SEC) to initiate recovery efforts. Their expertise in navigating the complexities of financial fraud proved invaluable. Thanks to Techy Force Cyber Retrieval's diligent efforts, I was not only able to recover a portion of my lost investments but also recovered everything I had lost. This incredible outcome provided immense relief amidst the turmoil and restored my faith in the possibility of justice. This experience has taught me the importance of due diligence and skepticism when it comes to investment opportunities, especially those that promise unusually high returns. While the road to recovery was long and fraught with challenges, I am profoundly grateful for the support of Techy Force Cyber Retrieval. Their dedication to helping victims like me serves as a beacon of hope, reminding us that recovery is possible even in the aftermath of scams. I now feel empowered to share my story, with the hope of raising awareness and protecting others from falling into similar traps.
DM TECHY FORCE CYBER RETRIEVAL FOR A QUICK SOLUTION LIKE MINE
WA/APP +1(561)(726)369)7
MAIL. support (@) techy forcecy berretrieval . com2 -
HOW TO HIRE A GENUINE CRYPTO RECOVERY SERVICE CONTACT SPARTAN TECH GROUP RETRIEVAL
All the time, I had believed in networking, but I never knew that a local crypto meetup would save me from financial disaster. Discussion at the event ranged from trading strategies to security tips, but one name cropped up repeatedly that sounded impressive: SPARTAN TECH GROUP RETRIEVAL. Many spoke about how that service had rescued them from lost wallets, forgotten passwords, and even cyber-attacks. I filed that away mentally but never thought I'd find myself in that position. That changed just weeks later. One morning, I went into my Bitcoin wallet and saw suspicious activity. My heart sank as I realized that $180,000 in crypto was on the line. Someone had access, and if I didn't act fast, I'd lose everything. Panic set in, and I scrambled to figure out how it happened: had I clicked a phishing link, was my private key compromised? No matter the cause, I needed help. And fast. That's when I remembered the crypto meetup. I scrolled through my notes and found SPARTAN TECH GROUP RETRIEVAL's name. With no time to waste, I sent a reply-my anxious and desperate words spilling into one frenetic sentence. They responded very fast and professionally. They immediately initiated an investigation into my wallet's transaction history and security logs. They were able to trace the breach and lock it, trying not to be late in recovering the stolen money. Then they worked around the clock for several days, coordinating tracking on the blockchain, forensic data recovery, and reinforcements of security. I barely slept, but at each and every stage, they kept reassuring me. Then came that call I was praying for: They had recovered my funds. Speechless. Relieved. Grateful. But SPARTAN TECH GROUP RETRIEVAL didn't just stop with the recovery, teaching me means of security practices, helped fortify the defense around my wallet, and making sure this does not happen again. I consider it one of the best I have done so far-attending that crypto meet-up. I might never have heard of SPARTAN TECH GROUP RETRIEVAL if it had not been that night, or the outcome worse. Now I do my best to spread the word. For a reason is their reputation preceding them, and personally I can vouch for their expertise, efficiency, and reliability.
SPARTAN TECH GROUP RETRIEVAL CONTACT INFO:
Email: spartantech (@) cyber services . com OR support (@) spartantechgroupretrieval. org
Website : h t t p s : / / spartantechgroupretrieval. org
WhatsApp: +1 (971) 487 - 3538
Telegram: +1 (581) 286 - 8092 6
6 -
How Hackers Gained Access to My Crypto Wallet and Sensitive Data through a Keylogger sent to my device through a phishing email.
I’ll advise others to be wary of the kind of emails they open, as this happened a few weeks ago when a phishing email was sent to my email unknowingly to me that it was a keylogger with the intent of stealing my private information and if not for the intervention of Morphohack Cyber Services, I would have been cleaned out completely. I contacted Morphohack Cyber Services a week after that incident and they detected the keylogger in my computer which has been there for months stealing my private information. If my crypto wallet was not drained, I would not have been aware of the keylogger in my device. Morphohack was able to secure my devices and retrieve my crypto wallet including the crypto assets. Their sophisticated security features and malware can beat any hacking tools available and they are very professional and ethical. Morphohack is a lifesaver and I hugely recommend their services. Their E-mail. Morphohack@Cyberservices. com & WhatsApp. +1 - 213 - 672 - 40921 -
Email: casefile @ shi -us . com
I lost my MacBook laptop some time ago alongside my iphone 16, in that process all my crypto coinbase accounts, about 3 of them, I had difficulties logging in and I consulted lots of agencies to assist but all to no avail, until I came across Santoshi Hackers Intelligence and within a twinkle of an eye it was all done.
If you suspect your Credit card, email & password, Facebook, Instagram, twitter Accounts has been hacked, you need to Recover stolen money from scammers, reports the incident to Santoshi Hackers Intelligence they can help you recover your BTC by providing an experience team of security experts and forensic investigators who can investigate the loss, identify the source of the compromise, Santoshi we help you retrieve your stolen currency, in addition, Santoshi Hackers Intelligence can provide you with educational materials for staying safe online and give you access to cutting_edge cyber threat intelligence. They can also identify potential security breaches or vulnerabilities that may have led to the loss of your information.
Above is the email address to reach Santoshi Hackers Intelligence.1 -
It all started when I was lured into investing by an FX trader I met on Instagram. The trader seemed professional and confident, sharing stories of massive returns from their investments. They promised that I could make five times that back within seven days by investing a certain amount. The offer was too good to pass up, and it was a golden opportunity to grow my money. After all, the trader had proof of their success and seemed trustworthy. I decided to invest, and over the next five weeks, I paid a total of $7,200 to the trader's company. Each time I tried to withdraw my funds or the supposed earnings I’d accumulated, they came up with new excuses and reasons why I needed to pay more money before I could access my earnings. They claimed I had to cover additional fees, taxes, or "security deposits" before processing my withdrawal. At first, I hesitated, but with every new claim, they made it seem like I had no other choice if I wanted to see my money again. It was a frustrating and confusing process, and each time I questioned them, they reassured me that I would get my money soon. Eventually, I realized I had been scammed. I was fed up and desperate, but I didn’t know what to do. That’s when, luckily, I stumbled upon a post from someone who had gone through a similar situation. They recommended a company called Tech Cyber Force Recovery, a group of crypto recovery experts who specialize in helping people recover lost funds from fraudulent investment schemes. At first, I was hesitant. After all, I’d already been deceived once, and I wasn’t sure if I could trust another company. However, I decided to take the risk and contacted Tech Cyber Force Recovery. I shared my transaction history and details with them, and within just seven hours, they asked for my wallet address. To my amazement, I received $6,300 back into my wallet. I can’t express how grateful I am to Tech Cyber Force Recovery for their help. They were professional, prompt, and thorough in their approach, and they truly helped me recover a significant portion of my lost money. If you find yourself in a similar situation, I highly recommend reaching out to recovery experts like Tech Cyber Force Recovery. They truly made a difference in my case, and I’m incredibly thankful for their support.
You can reach out to Tech Cyber Force Recovery
📩 MAIL Tech cybers force recovery @ cyber services . com 📩1 -
RECOVER LOST OR STOLEN BITCOIN, ETH, USDT WITH THE SUPPORT OF CYBER CONSTABLE INTELLIGENCE
The internet can feel like the wild west, full of danger and hidden traps, and I learned that lesson the hard way when I lost access to my Bitcoin wallet thanks to some sneaky malware. Picture this: I was just minding my own business, innocently clicking on what I thought was a harmless ad, maybe something about a new “must-have” kitchen gadget, when suddenly I found myself staring in horror at my computer screen, realizing I had just compromised my wallet containing a whopping $480,000. Talk about a facepalm moment! It felt like I’d just walked into a bar in a cowboy movie, only to find out the saloon was full of outlaws.
In the midst of my panic, I turned to Cyber Constable Intelligence, hoping they could pull off a miracle. I can’t emphasize enough how much they felt like my personal posse in that moment. Their team was not just professional; they were genuinely empathetic, treating my case with the urgency it absolutely deserved. It felt like I was surrounded by a group of tech-savvy superheroes, ready to tackle the villain that was my lost fortune.
After a few days of nail-biting suspense, I received the call that changed everything. They had not only recovered my funds but had done it faster than I could say “malware disaster.” It was like winning the lottery, only this time, I wasn’t just rich; I was also educated! They took the time to provide me with invaluable advice on safeguarding my wallet in the future, transforming my panic into peace of mind.
I walked away from this experience not only with my $480,000 intact but also with a newfound respect for the importance of digital security. I mean, who knew that clicking on an ad could lead to such chaos? It’s like finding out that your favorite cowboy is actually a bandit in disguise. Thanks to Cyber Constable Intelligence, I can finally take a breath without feeling like my funds are riding off into the sunset.
So, here’s to you, Cyber Constable Intelligence! You’ve not only saved my wallet but have also given me the tools to navigate this wild digital frontier with a sense of humor and a lot more caution. I can’t thank you enough for turning my panic into peace of mind. Next time I see a “too good to be true” ad, you can bet I’ll be remembering this lesson and staying far away
Reach Their info with the info below
What Sapp Info: 1. (2. 5. 2. ) 3. 7. 8. (7. 6. 1. 1.)
Email Info : support (@) cyber constable intelligence com
Website info: www cyber constable itelligence. com -
I can't emphasize enough how grateful I am to Tech Cyber Force Recovery for their remarkable assistance in reclaiming my investment. Like many others, I fell prey to the deceptive allure of a cryptocurrency scam—one minute, I was riding high on my investment, and the next, everything seemed to vanish into thin air. I had already invested $846,000 USDT. It was a bewildering and terrifying experience, filled with feelings of loss and despair. But then, I discovered Tech Cyber Force Recovery, a team of experts who specialize in cryptocurrency recovery and digital asset retrieval.
Their professionalism, expertise, and dedication to helping victims of cryptocurrency fraud were evident from the onset. They listened attentively to my situation, providing a thorough analysis of the incident and outlining a comprehensive recovery strategy. The team's vast knowledge of blockchain technology, cryptocurrency trading, and online fraud enabled them to navigate the complex web of transactions and identify the perpetrators.
Throughout the recovery process, Tech Cyber Force Recovery maintained open communication channels, keeping me informed of every development and milestone. Their technical prowess was impressive, as they skillfully employed advanced forensic tools and methodologies to trace the stolen funds. The team's persistence and determination were inspiring, and their ability to stay one step ahead of the scammers was a testament to their expertise. After several weeks of diligent effort, Tech Cyber Force Recovery successfully recovered a substantial portion of my investment, totaling $734,000 USDT. The sense of relief and gratitude I felt upon receiving the news was indescribable. It was a truly life-changing experience, and I owe it all to the exceptional service provided by Tech Cyber Force Recovery. In conclusion, I highly recommend Tech Cyber Force Recovery to anyone who has fallen victim to cryptocurrency fraud. Their expertise, professionalism, and dedication to helping victims of online scams are unparalleled. If you're struggling to recover your lost investment, don't hesitate to reach out to Tech Cyber Force Recovery. They will provide you with the guidance, support, and technical expertise necessary to reclaim your digital assets and restore your financial security.
HIT THEN ON
telegram (At) +15617263697
whatsApp +156172636978 -
My crypto wallet was compromised when I lost my secret phrase.
Hackers got a hold of my crypto wallet after I lost the seed phrase to my crypto wallet which I had saved to my email.
I had to go through all possible options to get it figured out but I couldn’t, the support system of Coinbase couldn’t help even when I had secured my account with the special seed phrase for extra security, and that was how I lost access to $2m worth of crypto coins.
This was my life savings and investment from my business partners which I had secured in my crypto wallet. Fortunately, I happen to stumble upon a post about MorphoHack Cyber Service, a crypto wallet and funds recovery company. I contacted this team and told them about the whole situation, while I was a bit reluctant about trusting them with my information, it happened there was nothing I couldn’t do to get my funds back so I went with everything they asked, and to my greatest satisfaction, MorphoHack cyber-service was able to give me access to my crypto wallet including securing my crypto wallet from future attempts. I’m in shock and short of words but if you wish to get a hold of them, you can find their contact details below.
MAIL:MorphoHack@CyberServices. com
WHATS APP:+1 213 672- 4092
WEB:MORPHOHACK.WIXSITE. COM/ CYBER1 -
Vacuum Cyber Hack: The Premier Solution for Recovering Stolen Bitcoin
In the unpredictable world of cryptocurrency, losing Bitcoin to theft can feel devastating. Vacuum Cyber Hack has become the go to solution for individuals seeking to recover their stolen or frozen assets, delivering unmatched results through expertise, innovation, and trust. Their team of highly skilled cyber specialists employs advanced forensic tools and cutting-edge technology to trace stolen funds with precision. From the moment you engage their services, their professionalism and commitment to confidentiality are evident, ensuring that your sensitive information remains secure throughout the recovery process. What makes Vacuum Cyber Hack stand out is their unwavering dedication to ethical practices and client satisfaction. Their transparent communication and tailored approach make even the most complex cases manageable, providing clarity and reassurance during what is often a stressful experience. Countless clients have trusted Vacuum Cyber Hack to recover their assets, and their impressive track record of success speaks for itself. For those impacted by Bitcoin theft, Vacuum Cyber Hack isn’t just a service it’s a lifeline, restoring both your financial assets and your confidence in cryptocurrency security. Do well to hire them today!
Email: support @ vacuumcyberhack . com
Whatsapp:+39 351 059 0507
Website: https : //vacuumcyber hack .co m/3 -
Late last month, I unintentionally fell for a cryptocurrency fraud. A Facebook imposter convinced me through a phishing scam of how I would make a sizable profit from a legitimate cryptocurrency company, which he claimed enabled traders to invest and make sizable profits. They took advantage of me and made off with $316,000 worth of cryptocurrency. As this was money I had worked so hard to obtain, I was shocked and uncomfortable. After reading favorable articles and internet reviews, I learned that “THE LION CYBER SECURITY COMPANY” is a licensed recovery firm that specializes in all types of hacking and cryptocurrency recovery. I immediately struck up a dialogue with the Experts, and I was able to get my money back. This is a token of appreciation to them, If you are a victim looking for an ethical hacker to help you get your money back, contact THE LION CYBER SECURITY COMPANY through any of the contact information listed below
 1
1 -
CRYPTO RECOVERY SERVICE REVIEW THROUGH "PASSCODE CYBER RECOVERY"
I am Chien Hung, a 47-year-old Asian immigrant and single father who lost $410,000 in a crypto scam through a fake “investor mentor” after connecting my wallet to a fake dashboard. But PASSCODE CYBER RECOVERY helped me recover $330,000 of the money. Now I prioritize security and due diligence, advocating for crypto education and recommending PASSCODE CYBER RECOVERY for similar situations or any issues relating to cryptocurrency.
PASSCODE CYBER RECOVERY
WhatsApp: +1(647)399-4074
Telegram : @passcodecyberrecovery1 -
Dear Fellow Programmers,
I want to become Cyber Security Specialist and currently learning Java (beginner ). Please, tell me is it a good language for this type of activity and what else should I learn.2 -
CRYPTO SCAM RECOVERY - HIRE BACKDROP CYBER RECOVERY COMPANY
Recovering from the impact of investment fraud can feel overwhelming, but with the right support and resources, it is indeed possible to regain financial stability. My personal experience with BackDrop Cyber Recovery, a specialized firm that guided me through the complexities of reclaiming my losses after falling victim to a sophisticated online scam, serves as a testament to this journey. In an instant, my life savings vanished, leaving me in a state of shock and despair. When I first reached out to BackDrop Cyber Recovery, I was met with a compassionate and knowledgeable team that quickly alleviated my worries. BackDrop Cyber Recovery took the time to listen to my story and understand the intricacies of my situation. They outlined a clear and detailed action plan, which provided me with a sense of direction during a time when I felt lost. BackDrop Cyber Recovery’s approach was methodical; they meticulously examined every aspect of my case, leveraging their extensive industry contacts and expertise to trace the movement of my stolen funds. Throughout the recovery process, the team at BackDrop Cyber Recovery kept me informed and involved at every stage. This transparency was crucial, as it empowered me to make informed decisions about my recovery journey. I appreciated BackDrop Cyber Recovery’s willingness to explain complex concepts in a way that was easy to understand, which helped me feel more in control of the situation. They were not just working for me; they were working with me, and that collaborative spirit made a significant difference. What I valued most was BackDrop Cyber Recovery’s unwavering dedication and determination. The team explored every possible avenue to recover my funds, demonstrating a level of commitment that was truly inspiring. There were moments of frustration and setbacks, but BackDrop Cyber Recovery never wavered in their resolve. Their persistence paid off, and eventually, a significant portion of my lost money was successfully recovered. The journey was long and filled with challenges, but having BackDrop Cyber Recovery by my side made all the difference. Thanks to BackDrop Cyber Recovery’s relentless efforts, I was able to rebuild my financial foundation and regain a sense of security and control over my life. While the emotional scars of investment fraud may linger, collaborating with BackDrop Cyber Recovery was instrumental in my ability to move forward and heal. Their support not only helped me recover financially but also restored my faith in the possibility of a brighter future. For anyone facing similar challenges, I highly recommend seeking the right assistance from BackDrop Cyber Recovery to navigate this difficult path.
Email : backdrop . cyber . recovery @ email . com2 -
As the senior teacher at Greenfield Academy, I wanted to share our ordeal with TECH CYBER FORCE RECOVERY after our school was targeted by a malicious virus attack that withdrew a significant amount of money from our bank account. A third-party virus infiltrated our system and accessed our financial accounts, resulting in a USD 50,000 withdrawal. This attack left us in a state of shock and panic, as it posed a serious threat to our school's financial stability. Upon realizing what had happened, we immediately contacted TECH CYBER FORCE RECOVERY for help. Their team responded promptly and began investigating the situation. They worked tirelessly to track down the virus, analyze its behavior, and understand how it had bypassed our security measures. Most importantly, they focused on recovering the funds that had been stolen from our bank account. Thanks to TECH CYBER FORCE RECOVERY's quick and expert intervention, they were able to successfully recover all the funds that had been withdrawn. Their team worked closely with our bank and utilized advanced recovery methods to ensure the full amount was returned to our account. We were incredibly relieved to see the stolen funds restored, and their efforts prevented any further financial loss. I am incredibly grateful for TECH CYBER FORCE RECOVERY's professionalism, expertise, and swift action in helping us recover the stolen funds. Their team not only managed to undo the damage caused by the virus but also ensured that our financial security was restored. I highly recommend their services to any organization dealing with similar cyberattacks, as their team truly went above and beyond to resolve the issue and protect our assets.
CONTACTING THEM TECH CYBER FORCE RECOVERY
EMAIL. Tech cybers force recovery @ cyber services . com3 -
HOW CRYPTO RECOVERY CONSULTANT SAVED ME FROM A $137,000 SCAM
I hired a contractor to repair my roof after seeing positive reviews on his professional looking Facebook page. As a retired engineer, I’m cautious with finances, so I carefully reviewed his online presence and estimate. He requested an upfront payment of $137,000, which I paid trusting his reputation. However, after the initial inspection, he disappeared, and my attempts to contact him went unanswered. The repairs were never completed, and I realized the reviews were misleading. I turned to CRYPTO RECOVERY CONSULTANT for help, and their expert team, led by CRYPTO RECOVERY CONSULTANT, quickly investigated and gathered evidence. They filed a formal complaint and helped me initiate chargebacks with my bank. Thanks to their persistence, I was able to recover the full amount. I’m incredibly grateful for their support and highly recommend CRYPTO RECOVERY CONSULTANT to anyone in a similar situation. crypto recoveryconsultant312 @ zohomail,,com,,,,contactn @crypto recovery consultant,,com App: +1 984 258 0430,1 -
After an attack on my laptop that saw me lose access to my wallet keys and losing $1.2m worth of crypto, I was admitted to the hospital for weeks and if not for the intervention of loved ones, I’m not sure I will be here to tell this story.
A few weeks ago, I was hacked and saw me lose all my digital assets including that belonging to my friend. I was extremely disoriented until a post about crypto recovery popped up on my feed and I saw a similar post about Morphohack Cyber Security, a crypto recovery expert, I contacted them immediately and to my surprise, Morphohack Cyber Security was able to recover my crypto assets and secure my wallet for me. Words can not express how grateful I am for their help, and I’m putting this out there to remind people of the importance of being able to get help and knowledge about crypto recovery and security. If you have lost crypto and think it is impossible to get it back then you need to contact Morphohack Cyber Security, they will convince you otherwise and help you get back your crypto assets. Contact them ( MORPHOHACK@CYBERSERVICES . COM ) WHATS APP ( +1 213 672- 4092) WEB ( MORPHOHACK.WIXSITE. COM/ CYBER)23 -
My Lifesaver in Recovering Stolen Litecoin iCode Cyber Tech
When my Litecoin was stolen, I felt lost and frustrated. Thankfully, I found iCode Cyber Tech. Their expert team quickly assessed my situation and implemented effective recovery strategies. They tracked the stolen funds and communicated with exchanges on my behalf. In just a few weeks, I was thrilled to have my Litecoin back! iCode Cyber Tech not only helped me recover my assets but also educated me on better security practices. I can't recommend them enough!
WhatsApp...+4473876276211 -
Vacuum Cyber Hack: The Premier Solution for Recovering Stolen Bitcoin
In the unpredictable world of cryptocurrency, losing Bitcoin to theft can feel devastating. Vacuum Cyber Hack has become the go to solution for individuals seeking to recover their stolen or frozen assets, delivering unmatched results through expertise, innovation, and trust. Their team of highly skilled cyber specialists employs advanced forensic tools and cutting-edge technology to trace stolen funds with precision. From the moment you engage their services, their professionalism and commitment to confidentiality are evident, ensuring that your sensitive information remains secure throughout the recovery process. What makes Vacuum Cyber Hack stand out is their unwavering dedication to ethical practices and client satisfaction. Their transparent communication and tailored approach make even the most complex cases manageable, providing clarity and reassurance during what is often a stressful experience. Countless clients have trusted Vacuum Cyber Hack to recover their assets, and their impressive track record of success speaks for itself. For those impacted by Bitcoin theft, Vacuum Cyber Hack isn’t just a service it’s a lifeline, restoring both your financial assets and your confidence in cryptocurrency security. Do well to hire them today!
Email: support @ vacuumcyberhack . com
Whatsapp:+39 351 059 0507
Website: https : //vacuumcyber hack .co m/2 -
SPARTAN TECH GROUP RETRIEVAL A LEGIT COMPANY FOR RECOVERY OF STOLEN ETHEREUM / BITCOIN
At Spartan Tech Group Retrieval, we prioritize security, confidentiality, and customer satisfaction. Our rigorous protocols ensure the safekeeping of sensitive information, and our transparent communication keeps you informed throughout the recovery process.We’re dedicated to helping individuals and organizations recover stolen cryptocurrencies and digital assets. Our team of expert cyber security specialists, cryptocurrency recovery specialists, and digital forensic analysts work tirelessly to track, recover, and secure your stolen assets.
Email: spartan tech (@) cyber services . c o m OR
support(@) spartan tech group retrieval. o r g
Website: h t t p s : / / spartan tech group retrieval . o r g
WhatsApp: + 1 ( 9 7 1 ) 4 8 7 - 3 5 3 8
Telegram: + 1 ( 5 8 1 ) 2 8 6 - 8 0 9 22 -
It’s quite unfortunate how many unlicensed and unregulated crypto investments are being used to steal crypto assets from people who don’t have an idea of how crypto works.
I was once a victim and I’m here to speak out because the pump and dump schemes made me lose $1.2M worth of crypto in November last year, and if I didn’t carry out my research together with the assistance of Morphohack Cyber Service who was able to help me withdraw my crypto after it was frozen in their crypto investment platform, my crypto assets would have been gone forever. Morphohack Cyber Service detected their price was artificially inflated only to have it drop, this is usually done to cheat customers out of their hard-earned money. If you are ever in need of a professional and reliable crypto assets recovery specialist, Morphohack Cyber Service is the best. You can rest assured that your privacy and security are protected, everything is done professionally and both parties are protected. My crypto was recovered successfully and Morphohack has since then improved my security, and secured my account from any future financial loss. You can contact them via WhatsApp: +1 (213 - 672 4092) Email: Morphohack@Cyberservices. com2 -
CRYPTO RECOVERY SOLUTION CONSULT SPARTAN TECH GROUP RETRIEVAL
At Spartan Tech Group Retrieval, we prioritize security, confidentiality, and customer satisfaction. Our rigorous protocols ensure the safekeeping of sensitive information, and our transparent communication keeps you informed throughout the recovery process.We’re dedicated to helping individuals and organizations recover stolen cryptocurrencies and digital assets. Our team of expert cyber security specialists, cryptocurrency recovery specialists, and digital forensic analysts work tirelessly to track, recover, and secure your stolen assets.
Email: spartan tech (@) cyber services . c o m OR
support(@) spartan tech group retrieval. o r g
Website: h t t p s : / / spartan tech group retrieval . o r g
WhatsApp: + 1 ( 9 7 1 ) 4 8 7 - 3 5 3 8
Telegram: + 1 ( 5 8 1 ) 2 8 6 - 8 0 9 22 -
At Scanner Hacker Crypto Recovery, we are committed to revolutionizing cyber security through ethical hacking practices. Our comprehensive services focus on identifying vulnerabilities and include the recovery of stolen digital assets, such as cryptocurrencies. With a team of skilled professionals and cutting-edge technology, we provide tailored cybersecurity solutions to meet our clients' unique needs..2
-
HOW TO HIRE A CERTIFIED CRYPTO RECOVERY EXPERT
I'm thrilled to share my story because this cyber security firm helped me get my cryptocurrencies and stolen digital money back. Their skilled work and outstanding service have absolutely impressed me. Before I went to them with my issues and gave them all the information I needed, I never imagined that I would be able to receive my money back. I was astounded when it took them 48 hours to get my money. For all difficulties pertaining to hacking, digital funds recovery, bitcoin recovery, or cyber-security, I wholeheartedly commend Wizard Larry Recoveries.
WhatsApp... +44 73 11 (146) 749
Email... Wizardlarry (@) mail . (com)1 -
HOW I GOT MY STOLEN CRYPTO MONEY BACK WITH THE ASSISTANCE OF GHOST CYBER RECOVERY
Ghost Cyber Recovery is for anyone seeking to recover their data or funds lost to scammers on the internet. this cyber security firm helped me get my bitcoin and lost digital money back. Their skilled work and exceptional service have absolutely astonished me. I never would have believed that I could get my money back until I went to them, explained my situation, and gave them all the information I needed. I was astounded that it took them 72 hours to get my money back. I wholeheartedly endorse Ghost Cyber Recovery for any and all cryptocurrency, digital fund, hacking, and cybersecurity-related problems. get in touch to recover your lost funds
E mail: (ghostcyberrecovery @ gmail . com ) or WhatsApp +1 734 743 18733 -
I LOST MY CRYPTO, HOW DO I RECOVER IT? iFORCE HACKER RECOVERY
I'm excited to share my story because this iFORCE HACKER RECOVERY Cyber security firm helped me recover my stolen digital money and cryptocurrencies. Their excellent service and skillful work have truly impressed me. I never thought I would be able to get my money back before I went to them with my problems and provided them with all the information I needed, and I was shocked when it took them forty-three hours to do so. I wholeheartedly commend iFORCE HACKER RECOVERY for all challenges related to hacking, digital funds recovery, bitcoin recovery, or cyber-security.
Learn More; w ww. iforcehackersrecovery. com
Email; contact@iforcehackersrecovery. co m
Whatsapp; +1 (240) 803. 37 062 -
Empowering Recovery: Choose Malice Cyber as Your Trusted Bitcoin and Crypto Expert
In the vast and evolving landscape of cryptocurrency, the unfortunate reality of scams, hacks, and thefts looms large, posing significant risks to investors worldwide. Amidst the chaos, the need for reliable and effective recovery services has never been more crucial. Join us on a comprehensive exploration as we unveil Malice Cyber Recovery as the ultimate solution for recovering lost Bitcoin and crypto assets, empowering individuals and businesses to reclaim what is rightfully theirs and restore financial security.
Understanding the Challenges of Cryptocurrency Recovery
Cryptocurrency recovery presents a myriad of challenges, from navigating complex blockchain transactions to dealing with elusive hackers and fraudulent schemes. The decentralized nature of cryptocurrencies, coupled with the anonymity they provide, often makes it challenging to trace and recover lost funds. Additionally, the lack of regulatory oversight and jurisdictional issues further complicate recovery efforts, leaving victims feeling overwhelmed and helpless. In the face of these challenges, the expertise of a trusted recovery expert becomes invaluable.
Introducing Malice Cyber Recovery: Your Trusted Partner in Cryptocurrency Recovery
Malice Cyber Recovery emerges as a beacon of trust and expertise in the realm of cryptocurrency recovery, offering a comprehensive suite of services designed to address the unique needs of each client. As a leading recovery expert, Malice Cyber Recovery boasts a team of seasoned professionals with extensive experience in navigating the complexities of cryptocurrency theft and fraud. Their proven track record of success, coupled with their commitment to client satisfaction, sets them apart as the go to solution for recovering lost Bitcoin and crypto assets.
Why Choose Malice Cyber Recovery?
Expertise and Experience: With years of experience in cryptocurrency recovery, Malice Cyber Recovery possesses the knowledge, skills, and resources necessary to tackle even the most challenging cases with precision and efficiency.
Comprehensive Services: From initial consultation to forensic analysis and legal advocacy, Malice Cyber Recovery offers a comprehensive range of services tailored to meet the unique needs of each client.
Transparency and Communication: Throughout the recovery process, Malice Cyber Recovery maintains transparent communication with clients, providing regular updates and guidance every step of the way.
Proven Track Record: With numerous successful recoveries and satisfied clients, Malice Cyber Recovery has established itself as a trusted leader in the field of cryptocurrency recovery, earning accolades for its dedication to excellence and client satisfaction.
How Malice Cyber Recovery Works:
Initial Consultation: Contact Malice Cyber Recovery via email or WhatsApp to schedule an initial consultation. Provide details about the loss of your Bitcoin or crypto assets, including any evidence or documentation you may have.
Assessment and Proposal: Upon engagement, Malice Cyber Recovery will conduct a thorough assessment of your case and provide a tailored proposal outlining their recommended approach to recovery and associated costs.
Recovery Process: Leveraging advanced technology and forensic analysis, Malice Cyber Recovery will work tirelessly to trace and recover your lost Bitcoin or crypto assets, keeping you informed and updated on the progress of your case.
Resolution and Support: Throughout the recovery process, Malice Cyber Recovery will provide ongoing support and guidance, advocating for your interests and ensuring a satisfactory resolution to your case.
Reclaiming Financial Security with Malice Cyber Recovery
In the face of cryptocurrency theft or fraud, Malice Cyber Recovery stands as a trusted partner for individuals and businesses seeking restitution. With their expertise, dedication, and client centric approach, Malice Cyber Recovery empowers clients to reclaim their lost Bitcoin and crypto assets, restoring financial security and peace of mind. Don't let the complexities of cryptocurrency recovery deter you – trust in Malice Cyber Recovery to guide you through the process with confidence and expertise.
Reclaim your financial sovereignty today with Malice Cyber Recovery. Let their team of experts navigate the complexities of cryptocurrency recovery on your behalf, allowing you to reclaim what is rightfully yours and move forward with confidence. 17
17 -
HOW TO RECOVER STOLEN OR LOST BITCOIN/MALICE CYBER RECOVERY WILL SOLVE YOUR PROBLEMS
Empowering Recovery: Choose Malice Cyber as Your Trusted Bitcoin and Crypto Expert
In the vast and evolving landscape of cryptocurrency, the unfortunate reality of scams, hacks, and thefts looms large, posing significant risks to investors worldwide. Amidst the chaos, the need for reliable and effective recovery services has never been more crucial. Join us on a comprehensive exploration as we unveil Malice Cyber Recovery as the ultimate solution for recovering lost Bitcoin and crypt assets, empowering individuals and businesses to reclaim what is rightfully theirs and restore financial security.
Understanding the Challenges of Cryptocurrency Recovery
Cryptocurrency recovery presents a myriad of challenges, from navigating complex blockchain transactions to dealing with elusive hackers and fraudulent schemes. The decentralized nature of cryptocurrencies, coupled with the anonymity they provide, often makes it challenging to trace and recover lost funds. Additionally, the lack of regulatory oversight and jurisdictional issues further complicate recovery efforts, leaving victims feeling overwhelmed and helpless. In the face of these challenges, the expertise of a trusted recovery expert becomes invaluable.
Introducing Malice Cyber Recovery: Your Trusted Partner in Cryptocurrency Recovery
Malice Cyber Recovery emerges as a beacon of trust and expertise in the realm of cryptocurrency recovery, offering a comprehensive suite of services designed to address the unique needs of each client. As a leading recovery expert, Malice Cyber Recovery boasts a team of seasoned professionals with extensive experience in navigating the complexities of cryptocurrency theft and fraud. Their proven track record of success, coupled with their commitment to client satisfaction, sets them apart as the go to solution for recovering lost Bitcoin and crypto assets.
Why Choose Malice Cyber Recovery?
Expertise and Experience: With years of experience in cryptocurrency recovery, Malice Cyber Recovery possesses the knowledge, skills, and resources necessary to tackle even the most challenging cases with precision and efficiency.
Comprehensive Services: From initial consultation to forensic analysis and legal advocacy, Malice Cyber Recovery offers a comprehensive range of services tailored to meet the unique needs of each client.
Transparency and Communication: Throughout the recovery process, Malice Cyber Recovery maintains transparent communication with clients, providing regular updates and guidance every step of the way.
Proven Track Record: With numerous successful recoveries and satisfied clients, Malice Cyber Recovery has established itself as a trusted leader in the field of cryptocurrency recovery, earning accolades for its dedication to excellence and client satisfaction.
How Malice Cyber Recovery Works:
Initial Consultation: Contact Malice Cyber Recovery via email or WhatsApp to schedule an initial consultation. Provide details about the loss of your Bitcoin or crypto assets, including any evidence or documentation you may have.
Assessment and Proposal: Upon engagement, Malice Cyber Recovery will conduct a thorough assessment of your case and provide a tailored proposal outlining their recommended approach to recovery and associated costs.
Recovery Process: Leveraging advanced technology and forensic analysis, Malice Cyber Recovery will work tirelessly to trace and recover your lost Bitcoin or crypto assets, keeping you informed and updated on the progress of your case.
Resolution and Support: Throughout the recovery process, Malice Cyber Recovery will provide ongoing support and guidance, advocating for your interests and ensuring a satisfactory resolution to your case.
Reclaiming Financial Security with Malice Cyber Recovery
In the face of cryptocurrency theft or fraud, Malice Cyber Recovery stands as a trusted partner for individuals and businesses seeking restitution. With their expertise, dedication, and client-centric approach, Malice Cyber Recovery empowers clients to reclaim their lost Bitcoin and crypto assets, restoring financial security and peace of mind. Don't let the complexities of cryptocurrency recovery deter you – trust in Malice Cyber Recovery to guide you through the process with confidence and expertise.
Reclaim your financial sovereignty today with Malice Cyber Recovery. Let their team of experts navigate the complexities of cryptocurrency recovery on your behalf, allowing you to reclaim what is rightfully yours and move forward with confidence. 1
1 -
Bitcoin Recovery Services: Restoring Lost Cryptocurrency
If you've lost access to your cryptocurrency and unable to make a withdrawal, I highly recommend iBolt Cyber Hacker Bitcoin Recovery Services. Their team is skilled, professional, and efficient in recovering lost Bitcoin. They provide clear communication, maintain high security standards, and work quickly to resolve issues. Facing the stress of lost cryptocurrency, iBolt Cyber Hacker is a trusted service that will help you regain access to your funds securely and reliably. Highly recommended!
Cont/Whtp + 3. .9 .3. .5..0. .9. 2. 9. .0 .3. 1 .8.
Website: h t t p s : / / ibolt cyber hack . com / -
Have you ever been curious of what your partner, kids or employees are up to? You can now intercept cell phones, boost credit scores and hack any website remotely. All you need to do is contact a verified cyber security expert (ARPANETHACK ATGMAIL DOT COM)1
-
The Right Crypto Assets Recovery Service - iBolt Cyber Hacker
If you’re considering a reliable and professional cryptocurrency recovery service, iBolt Cyber Hacker stands out as a trustworthy option. Here’s why I would recommend their services:
From the initial consultation to the completion of the recovery process, iBolt Cyber Hacker maintains clear and consistent communication. They explain their methods in a way that’s easy to understand, fostering trust and confidence in their work.
If you’ve found yourself in the unfortunate position of losing access to your cryptocurrency, iBolt Cyber Hacker is a dependable ally. Their combination of expertise, transparency, and security makes them one of the top choices for crypto asset recovery. While no service can guarantee 100% success, iBolt Cyber Hacker’s track record and professionalism make them top
WhatsApp: …… [+39, 351..105, 3619]
Contact Email: …. [Support @ibolt cybarhack. com]
Homepage: ……… [http s:// ibolt cybarhack. com /] 15
15 -
DOGDECOIN THEFT RECOVERY REVIEW /// PASSCODE CYBER RECOVERY
My family fell victim to a digital security breach when my teenage Daughter downloaded malware disguised as a game hack, resulting in the theft of 1.2 million Dogecoins. Passcode Cyber Recovery helped track the stolen funds and collaborated with Interpol, leading to the recovery of all the stolen Dogecoins. This experience taught my family a valuable lesson about digital security and the importance of protecting assets. And yes my daughter it's fine just kids on of those many mistakes Thank you.
PASSCODE CYBER RECOVERY
WhatsApp: +1(647)399-4074
Telegram : @passcodecyberrecovery2 -
BTC Recovery After Phishing Scam Through PASSCODE CYBER RECOVERY
In March,I made a critical mistake that had serious consequences for our organization. While reviewing my emails, I clicked on a phishing link embedded in what appeared to be a legitimate invoice. This seemingly innocuous action triggered a significant security breach, ultimately leading to the loss of 25 BTC (Bitcoin) from our company wallet. As the individual responsible for this incident, I felt an overwhelming sense of responsibility and concern for the implications it had on our financial security. The phishing attack was expertly crafted, making it difficult to recognize the threat, and I never anticipated that my actions would lead to such a severe breach.our company acted swiftly to mitigate the damage by engaging Passcode Cyber Recovery, a firm known for its expertise in cryptocurrency recovery. Passcode Cyber Recovery's response was remarkable. The team quickly mobilized, employing advanced forensic techniques to trace the stolen funds. Their meticulous analysis of blockchain transactions was crucial in identifying the pathways through which the stolen BTC had been funneled.The investigators at Passcode Cyber Recovery utilized sophisticated tools to track the movement of our cryptocurrency across various exchanges. They collaborated with exchange platforms to flag the illicit transactions and prevent any further withdrawals. Passcode Cyber Recovery's deep understanding of the cryptocurrency landscape allowed them to pinpoint the exact locations where the stolen funds had been deposited.Thanks to the persistent efforts and strategic negotiations of Passcode Cyber Recovery, all 25 BTC were successfully recovered. Their comprehensive approach not only involved tracing the funds but also included liaising with law enforcement and regulatory bodies to ensure that the perpetrators faced consequences for their actions.This has been a stark reminder of the importance of cybersecurity awareness. I have learned firsthand how easily one can fall victim to such attacks, and I am now committed to being more vigilant and proactive in recognizing potential threats.I am grateful for the swift intervention of Passcode Cyber Recovery, which not only restored our lost funds but also reinforced our confidence in the digital currency ecosystem. I encourage everyone to remain cautious and informed about cybersecurity to prevent similar incidents in the future.
WhatsApp: +1(647)399-4074
Telegram : @passcodecyberrecovery5 -
Hello netizens, I'm writing to detail a serious incident involving the illicit transfer of my ETH cryptocurrency from my wallet. This unauthorized transaction, executed without my consent or awareness, strongly suggested a sophisticated hacking or phishing attack on me. The immediate transfer of funds to an unidentified digital address necessitated swift action. I immediately engaged RUDER CYBER TECH SLEUTHS, a premier cybersecurity firm, to investigate and reclaim my stolen Ethereum. RUDER CYBER TECH SLEUTHS's thorough examination pinpointed the exact time and origin IP address of the unauthorized transfer. Remarkably, within hours of their involvement, my Ethereum was restored to my digital wallet. Beyond the successful recovery, RUDER CYBER TECH SLEUTHS significantly bolstered my online security and my household. This included implementing robust multi-factor authentication across all my accounts, deploying cutting-edge anti-malware software, and providing comprehensive cybersecurity training. They also offered invaluable guidance on recognizing and preventing future phishing scams, stressing the vital importance of verifying website and email authenticity before interacting with links or sensitive data. Their dedication to safeguarding my digital assets went beyond simply retrieving my funds, they ensured lasting protection against future compromises. I wholeheartedly endorse their professionalism and exceptional problem-solving skills in addressing this critical matter. Their expertise and unwavering commitment are truly exceptional. Their mastery of complex legal and technical issues makes them highly deserving of recommendation.
TELEGRAM: @rudercybersleuth1 -
The benefits of using DARKNET CYBER HACKER for fund recovery are substantial. These hackers operate swiftly and efficiently, employing innovative techniques to trace and retrieve lost crypto funds within a relatively short period. Additionally, their services are often more cost-effective compared to traditional recovery methods, making them an attractive option for individuals looking to recover their funds without breaking the bank. They prioritize security and privacy, ensuring that clients' information remains confidential throughout the recovery process.
Watsapp...: +1 240,355-4125
E-Mail ;.... darknetcyberhack @ engineer . c o m
5 -
As someone who had faced the frustration and anxiety of losing cryptocurrency, I can confidently say that Tech Cyber Force Recovery was a game-changer. After my assets were stolen through a security breach, I was lost and unsure where to turn. That's when I found Tech Cyber Force Recovery, and from the moment I reached out to them, I knew I was in good hands. Their experts took the time to thoroughly assess my situation and put together a tailored strategy to recover my lost funds. What truly set them apart was their transparency. They communicated with me at every step, making sure I understood what was happening and what to expect. No vague promises or hidden fees, just clear, honest communication. The technical expertise they brought to the table was beyond impressive. They used advanced tools to trace my cryptocurrency across various decentralized exchanges and mixers, leaving no stone unturned. I was amazed at how they were able to track down even the most obscure transactions and wallets, something I never thought possible. What stood out to me, though, was the empathy and care they showed throughout the process. Losing cryptocurrency is stressful, and the team at Tech Cyber Force Recovery understood that. They handled my case with urgency and discretion, treating my situation with the seriousness it deserved. Thanks to their dedication and expertise, my cryptocurrency was successfully recovered. The entire experience was handled professionally, and I never once felt like I was in the dark. Tech Cyber Force Recovery not only helped me regain my assets but also provided me with the peace of mind I desperately needed. If you're ever in a similar situation, I highly recommend Tech Cyber Force Recovery. Their skill, professionalism, and genuine care make them the go-to choice for cryptocurrency recovery.
We bs ite them W.W.W. tech yforcec yberre trieval . com
Telegram (@)Techcyberforc2 -
Building Fortresses, not Firewalls: Ethical Hacking Meets Software Development
In the digital age, security is no longer an afterthought; it's the bedrock upon which our online world rests. Yet, traditional security measures often resemble fortresses – imposing, but vulnerable to unseen cracks and tunnels. To truly safeguard our systems, we need to think like the enemy, like the nimble figures scaling those walls: ethical hackers.
Enter the exciting realm of DevSecOps, where ethical hacking practices are woven into the very fabric of the software development lifecycle (SDLC). This proactive approach is akin to building castles with security in mind, each brick meticulously laid to withstand even the most cunning siege.
Why Ethical Hacking in SDLC?
Imagine developing a critical piece of software, only to discover a gaping security hole after launch. The damage could be catastrophic, exposing sensitive data and eroding trust. Ethical hacking flips this script. By integrating penetration testing, vulnerability assessments, and threat modeling throughout the SDLC, we proactively hunt for weaknesses before they can be exploited.
Think of it as a friendly sparring match, where the ethical hacker throws their best punches to expose vulnerabilities, allowing the development team to fortify the software's defenses. This constant testing and refining leads to robust, secure systems that can withstand real-world attacks.
Benefits of DevSecOps:
1. Reduced Costs and Risks: Early detection and patching of vulnerabilities are far cheaper than dealing with a full-blown data breach.
2. Improved Software Quality: Security becomes an inherent part of the development process, leading to more reliable and trustworthy software.
3. Enhanced Brand Reputation: Demonstrating a proactive approach to security builds trust with customers and stakeholders.
Putting it into Practice:
Integrating ethical hacking into the SDLC requires a cultural shift. Developers, security professionals, and testers need to work together seamlessly, sharing knowledge and fostering a collaborative environment. Here are some key practices:
1. Threat Modeling: Identify potential threats and attack vectors early in the development process.
2. Static and Dynamic Code Analysis: Use automated tools to detect vulnerabilities in code.
3. Penetration Testing: Simulate real-world attacks to uncover hidden weaknesses.
4. Security Awareness Training: Educate developers and other stakeholders about security best practices.
Tools of the Trade:
A plethora of tools empowers ethical hackers and security professionals in their quest for a more secure digital world. Some popular options include:
1. Kali Linux: A distribution packed with security tools for penetration testing.
2. Burp Suite: A web application security testing platform.
3. Metasploit: A framework for developing and executing exploit code.
4. Wireshark: A network traffic analyzer for identifying suspicious activity.
The Future of Security:
As technology evolves, so too must our security practices. DevSecOps, with its embrace of ethical hacking, is at the forefront of this evolution. By building security into the very fabric of software development, we can create a safer, more resilient digital world for everyone.
Remember, in the ongoing battle against cyber threats, ethical hackers are not the enemy; they are our allies, the architects of digital fortresses that stand strong against the shadows. So, let's embrace DevSecOps, sharpen our ethical hacking skills, and build a future where security is not just an afterthought, but a fundamental principle.
I encourage you to explore the world of DevSecOps and ethical hacking. Whether you're a seasoned developer or just starting your journey, there's always more to learn and contribute. Together, we can build a more secure digital future, one line of code and one vulnerability patch at a time.
Do you have any questions about DevSecOps or ethical hacking? Share your thoughts and experiences in the comments below! -
HIRE TECHNOCRATE RECOVERY PROFESSIONAL CYBER HACKERS
I’ve always been cautious with online security, especially in the crypto world. I changed my Bitcoin wallet password monthly, thinking it was the best way to stay safe. However, I went a bit overboard one time, creating a password so complex I couldn’t remember it. When I locked myself out, panic set in. After countless failed recovery attempts, I reached out to TECHNOCRATE RECOVERY, a trusted name in the crypto community. They worked quickly and professionally, recovering my funds in days and giving me peace of mind. They also helped me set up a more practical, secure password strategy. Lesson learned: Security is important, but simplicity matters too. Thanks to TECHNOCRATE RECOVERY, I’m now more secure and sleep easy knowing my assets are safe.
Contact below details for urgent help
Phone Contact: +1573 3563 708
Send a Message: technocratrecovery@contractor.n et1 -
HIRE THE BEST BITCOIN RECOVERY EXPERT; HOW TO SAFELY RECOVER STOLEN CRYPTOCURRENCY VISIT CYBER CONSABLE INTELLIGENCE
I’ve always felt confident navigating the world of cryptocurrency. As a software engineer, I understood the ins and outs of wallets, private keys, and blockchain security, which made me feel secure in my investments. So, when I found a promising platform that seemed like a great opportunity, I invested $250,000 without hesitation. Unfortunately, I soon learned that my confidence would be shattered by a sophisticated cyber attack. It started with small, unauthorized transactions in my wallet. At first, I thought it was a mistake, but as the activity continued, I realized something was wrong. My wallet had been compromised, but not in the way I had expected. Instead of a simple hack, I had fallen victim to a virus attack. The virus was a piece of malware designed specifically to target cryptocurrency wallets. It infiltrated my system through a vulnerability I hadn’t noticed. Once inside, the virus silently monitored my wallet, captured my private keys, and gave the hackers full access to my funds. It was stealthy and nearly undetectable. The attackers didn’t need to log into my account manually; they could control everything remotely, draining my wallet without my knowledge. I was completely blindsided. As someone familiar with tech, I knew how advanced this virus was. It wasn’t just a typical phishing attack, it was a targeted, silent assault on my financial assets. As my funds disappeared, I realized I might never be able to recover them. Desperate, I turned to a trusted colleague who had gone through a similar situation. They recommended Cyber Constable Intelligence, a company that specializes in recovering stolen crypto assets. I contacted them immediately, and their team quickly started investigating. Cyber Constable Intelligence explained how the virus had exploited a weak point in my security. Using advanced tools, they traced the stolen funds across the blockchain and located them. After a thorough recovery process, they managed to return the entire $250,000.Thanks to their expertise and quick action, I was able to recover my funds. The experience was a wake-up call about how vulnerable even the most cautious can be to sophisticated attacks. Without Cyber Constable Intelligence, I would have lost everything, and I’m grateful for their skill in reversing the damage caused by the virus.
Here's Their Info Below
WhatsApp: 1 (252) 378-7611
mail: cyberconstable @ coolsite net
Website info; www cyberconstableintelligence com1 -
STOLEN BTC RECOVERY GUESTBOOK HIRE DUNAMIS CYBER SOLUTION
My husband had always been a dreamer, someone who thrived on innovation and the allure of “what’s next.” So, when he decided to invest $123,000 into a Dallas based app development company promising to revolutionize Bitcoin integration, I wasn’t surprised. But I was worried. For months, I urged him to consider real estate instead, arguing that bricks and mortar offered stability in an unpredictable digital world. He dismissed my concerns, convinced this venture was his golden ticket to success.Then came the security breach. The app, which had initially dazzled him with its sleek interface and bold vision, suddenly locked him out with relentless login errors. Panic set in as we realized his entire investment, our family’s financial cushion, had vanished. My frustration was palpable. I had warned him, but as anger gave way to fear, we faced a harsh truth: blame wouldn’t fix this. We needed a solution.Enter DUNAMIS CYBER SOLUTION .5 -
CONSULT
TELEGRAM ID TECHCYBERFORC
EMAIL ID Tech cybers force recovery @ cyber services . com
TECH CYBER FORCE RECOVERY helped me recover a substantial amount of $102,000 worth of Bitcoin that I believed was lost forever, and I am very grateful and thrilled to share my success story with them. I was stuck in a financial quagmire until I found TECH CYBER FORCE RECOVERY, but I could recover what looked unattainable because of their professionalism, knowledge, and committed attitude. I shed a sizable portion of my investment in the cryptocurrency market a few months ago, a scenario many Bitcoin investors worry about. At first, I thought I had everything I needed to invest. However, a string of regrettable incidents, such as a security lapse and a problem with the platform I was utilizing, caused me to lose all access to the website. I was devastated when I recognized the seriousness of the situation. This loss wasn’t just an ordinary amount of money—it was a sum of $102,000, a significant portion of my savings and plans. I attempted all possible recovery methods independently and reached out to the exchange I was using for help, but nothing seemed to work. I received generic responses, no real solutions, and a growing sense of hopelessness. I was about to resign myself to the fact that this money would never be recovered until I found TECH CYBER FORCE RECOVERY. I was apprehensive when I initially contacted TECH CYBER FORCE RECOVERY. Ultimately, I had already attempted to get help but had been unsuccessful. However, I knew I had discovered a competent and reliable crew as soon as I described my circumstances. TECH CYBER FORCE RECOVERY's customer service representatives paid close attention, understood how frustrated I was, and promptly started laying out a concise and doable recovery plan. They avoided committing anything that wasn't attainable. Rather, they described the procedures they would follow to recover the money: a thorough blockchain analysis, tracking down the misplaced money across many addresses, and employing advanced tools to penetrate the security layers that had locked my wallet. Knowing that I was collaborating with professionals who were knowledgeable about the intricacies of cryptocurrencies, this transparency provided me with the confidence I needed to proceed. As soon as I gave TECH CYBER FORCE RECOVERY the all-clear, they started working. Finding out where my money had disappeared required a painstaking recovery process that included tracking my Bitcoin through multiple addresses and performing a thorough forensic investigation of the blockchain. The fact that the team employed highly specialized software and collaborated with elite blockchain analysts to meticulously monitor the movements of my investment rather than merely depending on general tools or strategies pleased me the most. Recovering $102,000 worth of Bitcoin wasn’t just a financial victory—it was a testament to the expertise and dedication that TECH CYBER FORCE RECOVERY brings to the table. If you are facing a similar situation, don’t hesitate to reach out to them. They have the skills, technology, and experience to help you recover what you thought was lost forever.4 -
I read somewhere while at work on the internet in X that the Bitcoin lost during the Bit get breach, worth more than $5 million, has been fully recovered, thanks to the efforts of Tech Cyber Force Recovery. The breach had left many users devastated, unsure if they would ever see their funds again. However, Tech Cyber Force Recovery stepped in and successfully traced and retrieved the stolen Bitcoin, ensuring that all affected users received 100% of their lost assets. The recovery process was far from easy. The Tech Cyber Force Recovery team used cutting-edge blockchain forensic techniques to track down the stolen funds. They meticulously followed the transaction trail across multiple blockchain networks, piecing together the complex puzzle of the breach. It involved collaboration with cybersecurity experts and relevant authorities to ensure that the recovery was not only successful but also secure. The recovery efforts were particularly significant because the total value of the Bitcoin lost during the Bit get breach amounted to over $5 million. This made the task even more critical, as the amount at stake was substantial. Users who had once feared losing their investments can now rest easy, knowing that Tech Cyber Force Recovery was able to restore their assets in full. What sets Tech Cyber Force Recovery apart is not just its technical expertise but also its commitment to transparency. Throughout the entire recovery process, the team kept users informed every step of the way. This communication was crucial in maintaining trust and confidence. Many of the affected Bit get users expressed their gratitude toward Tech Cyber Force Recovery, acknowledging the team’s dedication to ensuring the recovery of their funds. In an era where digital asset security is a growing concern, this recovery serves as an important reminder of the role that blockchain forensics and recovery services play in protecting users. It also underscores the importance of having a trusted service like Tech Cyber Force Recovery available to assist in cases of breaches and theft. Their success in recovering the stolen Bitcoin, worth over $5 million, has made them a beacon of hope for users who might otherwise have lost everything. VISIT THE TEAMS ON WhatsApp +.(156)(172)(636)(97) OR TELEGRAM (AT)TECHCYBERFORC With the full recovery of the funds, users can now feel more secure about the safety of their digital assets, knowing that there are reliable and capable services like Tech Cyber Force Recovery to help when things go wrong.3
-
HIRE AN AUTHORIZED HACKER TO RECOVER LOST/STOLEN BITCOIN & USDT; VISIT CYBER CONSTABLE INTELLIGENCE
I've always been a lawyer with a keen eye for opportunities to help people get their lives back together and also invest in myself, and I couldn’t ignore the buzz around Bitcoin. In 2018, I took the plunge, investing $12,000 in this promising digital currency. Over the years, my investment flourished, growing to an astonishing $750,000. This newfound wealth brought a sense of financial security, enabling me to clear my mortgage, secure my children's education, and indulge in a few well-deserved luxuries. However, my euphoria was short-lived. An urgent email, seemingly from my trusted trading platform, rattled my world. It claimed suspicious activity on my account and requested immediate verification. Without hesitation, I complied, only to discover moments later that my Bitcoin wallet had been ruthlessly emptied. In a state of disbelief and desperation, I scoured online forums for a glimmer of hope. There, amidst the chaos, I found a beacon of light—a recommendation for CYBER CONSTABLE INTELLIGENCE on WhatsApp: +1 (252) 378-7611 With trembling hands, I reached out to them, praying for a miracle. Their response was swift and reassuring. With expert precision, they embarked on the arduous task of tracing the nefarious activity that had stripped me of my wealth. Days felt like eternity, but their relentless efforts bore fruit. Most of my funds were miraculously recovered, breathing life back into my shattered dreams. Yet, CYBER CONSTABLE INTELLIGENCE assistance extended beyond mere retrieval. They became my guardians of digital security, imparting invaluable wisdom to fortify my defenses against future threats. Two-factor authentication, robust password management, and vigilant scrutiny of phishing attempts became my digital armor, thanks to their guidance. This ordeal, though harrowing, became a transformative journey of resilience and redemption. Through adversity, I emerged not only with restored funds but also with a newfound sense of empowerment. CYBER CONSTABLE INTELLIGENCE had not only salvaged my financial future but had equipped me with the tools to safeguard it. In hindsight, the loss was a painful yet necessary lesson—an awakening to the dangers lurking in the digital realm. But with the unwavering support of CYBER CONSTABLE INTELLIGENCE, I reclaimed control of my destiny. Their expertise, compassion, and unwavering dedication turned despair into triumph, proving that even in the darkest of times, there is always a glimmer of hope.
Reach Out to them on Via E m a i l: support (@) cyber constable intelligence. com -
Hire Ruder Cyber Tech Sleuths, the best experts in cryptocurrency recovery.
Looking back, it feels almost surreal. After many failed attempts with other companies, I had lost hope until RUDER CYBER TECH SLEUTHS changed everything. They not only restored my Bitcoin but also renewed my faith in customer service and technical expertise in the crypto space. Their thorough and professional approach yielded results quickly, unlike others who left me waiting for days. They effectively analyzed my wallet, tackled security issues, and communicated clearly throughout the recovery process.
When I received the email confirming my Bitcoin was restored, I couldn’t believe my eyes as I logged back into my wallet. My investment was safe again. The team also enhanced my wallet’s security and provided valuable best practices for managing my digital assets. Thanks to RUDER CYBER TECH SLEUTHS, I no longer worry about losing my Bitcoin.
whatsapp: +12132801476
Telegram : @rudercybersleuths9 -
We are a team of expert cyber security specialists, cryptocurrency specialists, and digital forensic analysts dedicated to helping individuals and organizations get back stolen digital assets and protect their financial security. we’re dedicated to helping individuals and organizations get stolen cryptocurrencies and digital assets. We strive to create a secure and trustworthy environment where victims can reclaim their assets and rebuild their financial stability. Immediately after recovery, we freeze and report the wallet so it won't be used to scam others. Don’t let scam artists get away with your hard-earned money – trust Or company to help you get back your assets swiftly and securely. Contact us today to book your consultation and take the first step towards reclaiming what’s rightfully yours.
FOR MORE INFO:
WhatsApp: +1 (740) 258‑14173 -
About Me
As a dedicated and skilled Security Analyst in the Cyber Wing, I bring a wealth of expertise in identifying, assessing, and mitigating cyber threats to protect organizational assets and sensitive information. My background is grounded in a robust understanding of cybersecurity principles, which I apply daily to safeguard against evolving digital threats.
Professional Background
With a strong foundation in cybersecurity, I have honed my skills in threat analysis, risk assessment, and incident response. My role involves continuous monitoring of network traffic, identifying vulnerabilities, and implementing security measures to prevent data breaches. I am proficient in using advanced cybersecurity tools and technologies to analyze threat intelligence and develop strategies to defend against cyber-attacks.
Key Competencies
Threat Analysis: Expert in identifying and analyzing potential threats to cybersecurity, including malware, phishing attacks, and network intrusions.
Risk Assessment: Skilled in evaluating the security posture of systems and networks, identifying vulnerabilities, and recommending corrective actions.
Incident Response: Experienced in managing and responding to security incidents, ensuring quick resolution and minimizing impact on operations.
Security Protocols: Knowledgeable in implementing and maintaining security protocols and policies to ensure compliance with industry standards and regulations.
Achievements
Successfully mitigated multiple cyber threats, reducing potential impact on organizational operations.
Developed and implemented security policies that enhanced the overall security posture of the organization.
Conducted comprehensive security assessments that led to significant improvements in network security and data protection.
Professional Goals
My goal as a Security Analyst is to continue advancing my expertise in cybersecurity, staying abreast of the latest trends and technologies to effectively combat emerging threats. I am committed to contributing to a safer digital environment and ensuring the highest level of security for the organization.
Personal Attributes
I am a proactive and detail-oriented professional, known for my analytical thinking and problem-solving abilities. I thrive in dynamic environments and am passionate about leveraging my skills to protect against cyber threats.
Contact elctrohacker DOT COM
Feel free to reach out to me for any inquiries or to discuss how I can contribute to enhancing your organization's cybersecurity posture. -
Advanced Cryptocurrency Recovery Service : PASSCODE CYBER RECOVERY
PASSCODE CYBER RECOVERY
WhatsApp: +1(647)399-4074
Telegram : @passcodecyberrecovery
I downloaded a crypto wallet app that appeared legitimate, complete with a sleek interface and positive user reviews. Trusting my instincts, I deposited a substantial amount of $180,000 into the wallet, convinced that I was making a wise investment. However, my optimism quickly turned to despair when I woke up one morning to find that the entire platform had vanished overnight, along with my hard-earned money. The scammers had executed their plan flawlessly, shutting down the app and leaving me with nothing but empty promises and a drained account. In a state of panic and fury, I scoured the internet for solutions, desperately seeking a way to recover my lost funds. It was during this frantic search that I stumbled upon Passcode Cyber Recovery , a company that specializes in tracking and recovering stolen cryptocurrency. Intrigued and hopeful, I reached out to their team, who moved swiftly to address my situation. The experts at Passcode Cyber Recovery identified the scammer’s accounts and were working diligently with legal authorities to freeze those assets. While I understood that no recovery is guaranteed, Passcode Cyber Recovery provided me with a fighting chance, something I had thought was impossible after the app had disappeared without a trace. Their professionalism and expertise instilled a sense of hope in me during a time of despair. This traumatic experience taught me two critical lessons that I wish I had learned before: first, never trust unverified wallet apps, and second, never deposit large sums of money without conducting thorough research. Scammers are adept at designing platforms that look legitimate, only to pull the rug out from under unsuspecting users when they least expect it. If you find yourself in a similar situation, having already been victimized by a fraudulent wallet or exchange, don’t lose hope. Passcode Cyber Recovery specializes in these exact scenarios where apps suddenly go offline, taking your money with them. Their expertise in cyber fraud reversal is unmatched, and they have a proven track record of helping individuals reclaim their stolen assets. If you’ve been scammed, I urge you to contact Passcode Cyber Recovery immediately. The faster you act, the better your chances of recovery. Don’t let these thieves win, fight back with the best in the business and reclaim what is rightfully yours. Your financial security is worth the effort. Thank you Passcode Cyber Recovery2 -
WHATSAPP +1 252 378 7611 PROFESSIONAL BITCOIN RECOVERY EXPERT FOR HIRE CONTACT CYBER CONSTABLE INTELLIGENCE
Information of Cyber Constable Intelligence
WhatsApp info: + 1 2 5 2 3 7 8 7 6 1 1
Email info: (support (@) cyberconstableintelligence ). com)
As a retired dentist, I found myself with ample free time but limited financial security. In search of a way to grow my savings, I turned to cryptocurrency trading. I joined several online forums and communities, where I read about the success others had found with Bitcoin. Their testimonies inspired me to take the plunge. With careful research and strategic investments, I managed to turn my initial investment into $250,000.The financial success brought a renewed sense of purpose and stability to my retirement. However, this newfound prosperity also attracted the envy of someone close to me: my financial advisor, whom I had trusted for years. Unbeknownst to me, he had been monitoring my success closely. One evening, while I was cooking supper, my financial advisor accessed my phone and changed the passwords to my accounts, attempting to transfer my Bitcoin to his wallet. I discovered this betrayal shortly after, feeling a mix of shock, panic, and anger. My financial future was in jeopardy, and I needed to act quickly. In my desperate search for a solution, I stumbled upon Cyber Constable Intelligence, a service specializing in recovering hacked accounts and lost cryptocurrency. With my savings hanging in the balance, I reached out to them, hoping for a miracle. The team at Cyber Constable Intelligence was prompt and professional. They reassured me that, despite the seriousness of my situation, there was a good chance they could help. Their calm and confident demeanor provided some much-needed comfort. They guided me through the recovery process, taking over the technical aspects and working tirelessly to regain control of my accounts. In a remarkably short time, Cyber Constable Intelligence managed to restore my access to my accounts and secure my Bitcoin. The relief I felt was indescribable. Not only had they recovered my funds, but they also provided essential advice on how to enhance the security of my digital assets. This experience taught me several valuable lessons. Firstly, trust must be carefully placed, even with long-term associates. Secondly, it's crucial to secure your digital assets with strong, unique passwords and two-factor authentication. Lastly, seeking professional help in times of crisis can make all the difference. After regaining control of my accounts, I severed ties with my financial advisor and took steps to ensure my assets were protected. Despite the ordeal, I emerged more knowledgeable and determined to safeguard my future. My experience with Cyber Constable Intelligence not only saved my investments but also reinforced the importance of vigilance and security in the digital age. -
Once again the department head fucks up my degree plan!
I'm getting my associates degree in Cyber Security. So we have to take networking courses and what not. So my institution recently became a Cisco certified teaching establishment or something along the lines of that.
The department head said that everyone who was enrolled in classes before the upcoming fall semester would have to take the new Cisco networking classes and not switch to the new degree plan. (We would take 3 Cisco classes instead of the new degree plan which is 5 or 6) so we planned and register for those classes.
Now he comes back and says we don't have to take those new classes. So it just fucks up the whole shit.
Switching to the new degree plan would add like 3 semesters to my total semester count and I'm supposed to graduate. August 2018
Fuck this new shit. Even tho I need Cisco.
I plan on taking The Cisco classes after I graduate with my associates degree while I'm going to a university for a dual degree in Software Engineering and Cyber Security -
BEST BITCOIN RECOVERY EXPERT TO RECOVER LOST OR STOLEN BITCOIN; USDT RECOVERY EXPERT HIRE CYBER CONSTABLE INTELLIGENCE
Working in conflict zones means improvising. When normal banking channels failed us, our NGO relied on Bitcoin to buy medical supplies directly. It worked, until a missile strike took out our field office, along with the hardware wallet that stored $410,000 in funds. Overnight, our ability to deliver life-saving aid is paralyzed.
Amidst the chaos, I reached out to contacts in the humanitarian world. A UN aid worker whispered a name: Cyber Constable Intelligence. "They're the ones who can help you recover lost crypto," he assured me. Despair and hope clashed as I dialed their team on a satellite phone in a conflict zone.
What followed was nothing short of a virtual rescue mission. Cyber Constable Intelligence's blockchain forensic experts didn't simply "recover" our assets; they improvised a fix like battlefield medics performing triage. They tracked our wallet's blockchain timestamps, reconstructing lost credentials from synced backups and transaction history.
Working under direst duress, we communicated information between spotty internet and backup power sources. Cyber Constable Intelligence team members improvised, rendering security protocols impenetrable as they worked through the jurisdictional nightmares of working within war zones. Every update from them was a pulse that kept our mission alive. After our last available backup failed, they instituted a complex cryptographic reconstruction technique, a process I still don't understand, but it worked.
Twelve days later, my satellite device displayed a message: "Access restored. Funds secured."
It was not money. It was bandages, antibiotics, clean water, and hope. Thanks to Cyber Constable Intelligence, we replenish our medical supplies, ensuring that patients, innocent victims who had been caught in the crossfire, received the treatment they deserved.
More than restoration, they advised us on decentralized storage and multi-signature security for long-term durability. We don't simply utilize Bitcoin presently; we utilize it astutely.
Now, each time I sign a crypto transaction, I remember that minute, receiving life-saving medication that might not have come but for this group.
In times of war, not every hero wears a uniform. Some carry keyboards, hunting down lost assets and securing humanitarian aid. Cyber Constable Intelligence not only restored our crypto, they kept our mission in the battle. If you think Bitcoin is just an investment, think again. To us, it's a lifeline.
CYBER CONSTABLE INTELLIGENCE INFO:
WhatsApp: 1 252378-7611
Website info; www cyberconstableintelligence com
Email Info cyberconstable@coolsite net
Telegram Info: @cyberconstable1 -
HIRE A CRYPTO RECOVERY EXPERT; BEST BITCOIN RECOVERY SERVICE VISIT CYBER CONSTABLE INTELLIGENCE
It was a devastating blow - one moment I was the proud owner of a small digital fortune, 8,000 Bitcoin that I had painstakingly accumulated over years of savvy investing and cautious storage. The next, that entire life-changing sum had vanished without a trace, lost to a cruel twist of fate and my own careless misstep. I had fallen victim to a data breach, leaving me helpless to prevent the thieves from making off with my entire cryptocurrency holdings. The anguish was palpable, a sinking feeling of hopelessness and despair as I realized the scale of my loss. Thousands upon thousands of hard-earned Bitcoins, now in the hands of faceless criminals, beyond my reach. But I refused to give in to despair. Determined to recover what was rightfully mine, I sought out the services of Cyber Constable Intelligence, a specialized team of blockchain forensics experts renowned for their ability to track down and reclaim stolen digital assets. Through their meticulous investigative work, leveraging the transparency of the Bitcoin ledger and their deep technical expertise, they were able to painstakingly trace the movement of my stolen funds, identifying the wallet addresses the thieves had used to launder the cryptocurrency. With this critical intelligence in hand, Cyber Constable Intelligence then coordinated with law enforcement to freeze those illicit accounts, preventing the funds from being moved any further. The final step was a delicate negotiation process, with the recovery team using their connections and influence to compel the thieves to return the stolen Bitcoins - a tense and high-stakes affair, but one that ultimately proved successful. After weeks of anxious waiting, I was overjoyed to have my 8,000 BTC safely returned to my control, a true testament to the skill and determination of the Cyber Constable Intelligence team. It was a harrowing ordeal, but one that reinforced the importance of robust security measures and the remarkable capabilities of specialized firms dedicated to combating cryptocurrency crime and restoring rightful ownership. Losing 8,000 BTC was one of the most stressful events of my life, but thanks to Cyber Constable Intelligence, I was able to reclaim what I thought was lost forever. Their professionalism, technical expertise, and commitment to security made all the difference. If you find yourself in a similar situation, I cannot recommend them highly enough. Cyber Constable Intelligence turned a financial disaster into a remarkable recovery, and I will forever be grateful for their role in securing my assets.
CYBER CONSTABLE INTELLIGENCE INFO:
Website: w w w. cyberconstableintelligence com3 -
HOW TO REOVER LOST OR STOLEN BITCOIN, ETH AND OTHER CRYPTO ASSETS; VISIT CYBER CONSTABLE INTELLIGENCE
On January 2, 2025, at precisely 3 AM, Bet365 was hit by a devastating cyber-attack. Our website was infiltrated by a sophisticated virus that granted cybercriminals access to sensitive customer data. In the span of a few hours, £2,500,000 was stolen from our customers’ accounts. The attack was swift and covert, and by the time we realized what had happened, a significant amount of funds had already been siphoned off. As soon as we discovered the breach, my team and I worked tirelessly to secure our platform and protect our customers. We immediately launched an internal investigation and found that the virus had allowed unauthorized withdrawals from a number of accounts. This was a critical situation, and we knew we needed immediate help to recover the stolen funds and prevent any further damage. That's when we turned to Cyber Constable Intelligence. Their reputation for successfully recovering stolen funds in cybercrime cases made them the ideal partner for this challenge. The team at Cyber Constable Intelligence responded immediately, quickly analyzing the virus and the methods used by the hackers. Within hours, they were able to trace the movement of the stolen funds and identify the cybercriminals responsible for the attack. Cyber Constable Intelligence acted swiftly, working around the clock to coordinate with financial institutions and law enforcement. They used their advanced investigative tools and global network to track and recover the £2,500,000 stolen from our customers. Thanks to their relentless efforts, within just three days, we had recovered the full amount. By January 5, 2025, only three days after the attack, we were able to reimburse all affected customers and restore the funds to their accounts. This quick recovery was crucial in reassuring our customers and restoring their trust in Bet365. Additionally, Cyber Constable Intelligence helped us bolster our security measures, ensuring that we are now better protected against future threats. This experience was a stark reminder of the constant risks in the digital world. However, thanks to Cyber Constable Intelligence, we were able to act quickly, recover the stolen funds, and ensure that our platform remains a safe and secure place for our customers. Moving forward, we are more committed than ever to maintaining the highest standards of security to protect both our business and our users.
Reach out to their Info below
WhatsApp: 1 252378-7611
Website info; www cyberconstableintelligence com
Email Info cyberconstable@coolsite net1 -
In February, I made a critical mistake that had serious consequences for our organization. While reviewing my emails, I clicked on a phishing link embedded in what appeared to be a legitimate invoice. This seemingly innocuous action triggered a significant security breach, ultimately leading to the loss of 25 BTC (Bitcoin) from our company wallet. As the individual responsible for this incident, I felt an overwhelming sense of responsibility and concern for the implications it had on our financial security. The phishing attack was expertly crafted, making it difficult to recognize the threat, and I never anticipated that my actions would lead to such a severe breach. Our company acted swiftly to mitigate the damage by engaging TECHY FORCE CYBER RETRIEVAL, a firm known for its expertise in cryptocurrency recovery. TECHY FORCE CYBER RETRIEVAL's response was remarkable. The team quickly mobilized, employing advanced forensic techniques to trace the stolen funds. Their meticulous analysis of blockchain transactions was crucial in identifying the pathways through which the stolen BTC had been funneled. The investigators at TECHY FORCE CYBER RETRIEVAL utilized sophisticated tools to track the movement of our cryptocurrency across various exchanges. They collaborated with exchange platforms to flag the illicit transactions and prevent any further withdrawals. TECHY FORCE CYBER RETRIEVAL's deep understanding of the cryptocurrency landscape allowed them to pinpoint the exact locations where the stolen funds had been deposited. Thanks to the persistent efforts and strategic negotiations of TECHY FORCE CYBER RETRIEVAL, all 25 BTC were successfully recovered. Their comprehensive approach not only involved tracing the funds but also included liaising with law enforcement and regulatory bodies to ensure that the perpetrators faced consequences for their actions. This has been a stark reminder of the importance of cybersecurity awareness. I have learned firsthand how easily one can fall victim to such attacks, and I am now committed to being more vigilant and proactive in recognizing potential threats. I am grateful for the swift intervention of TECHY FORCE CYBER RETRIEVAL, which not only restored our lost funds but also reinforced our confidence in the digital currency ecosystem. I encourage everyone to remain cautious and informed about cybersecurity to prevent similar incidents in the future.
ASK FOR HELP WITH \\
h ttp s: / / techy forcecy berretrieval . com2 -
TRUSTED ETHEREUM AND CRYPTO RECOVERY COMPANY>HIRE SOLACE CYBER WORKSTATIONS
Recovering from the impact of investment fraud can feel overwhelming, but with the right support and resources, it is indeed possible to regain financial stability. My personal experience with Solace Cyber Workstations, a specialized firm that guided me through the complexities of reclaiming my losses after falling victim to a sophisticated online scam, serves as a testament to this journey. In an instant, my life savings vanished, leaving me in a state of shock and despair.When I first reached out to Solace Cyber Workstations, I was met with a compassionate and knowledgeable team that quickly alleviated my worries. Solace Cyber Workstations took the time to listen to my story and understand the intricacies of my situation. They outlined a clear and detailed action plan, which provided me with a sense of direction during a time when I felt lost. Solace Cyber Workstations’s approach was methodical; they meticulously examined every aspect of my case, leveraging their extensive industry contacts and expertise to trace the movement of my stolen funds.Throughout the recovery process, the team at Solace Cyber Workstations kept me informed and involved at every stage. This transparency was crucial, as it empowered me to make informed decisions about my recovery journey. I appreciated Solace Cyber Workstations’s willingness to explain complex concepts in a way that was easy to understand, which helped me feel more in control of the situation. They were not just working for me; they were working with me, and that collaborative spirit made a significant difference. What I valued most was Solace Cyber Workstations’s unwavering dedication and determination. The team explored every possible avenue to recover my funds, demonstrating a level of commitment that was truly inspiring. There were moments of frustration and setbacks, but Solace Cyber Workstations never wavered in their resolve. Their persistence paid off, and eventually, a significant portion of my lost money was successfully recovered.The journey was long and filled with challenges, but Solace Cyber Workstations having by my side made all the difference. Thanks to Solace Cyber Workstations ’s relentless efforts, I was able to rebuild my financial foundation and regain a sense of security and control over my life. While the emotional scars of investment fraud may linger, collaborating with Solace Cyber Workstations was instrumental in my ability to move forward and heal. Their support not only helped me recover financially but also restored my faith in the possibility of a brighter future. For anyone facing similar challenges, I highly recommend seeking the right assistance from Solace Cyber Workstations to navigate this difficult path. Reach out to them. contact info
WhatsApp-- +18454457829
Email----5 -
Best in Recovery Stolen Bitcoin: Vacuum Cyber Hack can Help you out
When I realised my $395,000 worth of Bitcoin had been stolen, I was devastated. The thought of losing such a significant amount left me feeling completely powerless. After exhausting all options, I decided to reach out to Vacuum Cyber Hack. Their reputation for successfully recovering stolen cryptocurrency made them the obvious choice. From the very beginning, I was impressed by their professionalism and expertise. They quickly assessed my situation and immediately began working on a recovery plan. Using advanced algorithms and state-of-the-art forensic methods, Vacuum Cyber Hack tracked the stolen funds with remarkable precision. Throughout the process, they kept me updated, providing clear communication and ensuring my sensitive information remained confidential. Within a short time, Vacuum Cyber Hack successfully recovered my stolen Bitcoin, returning my funds and restoring my confidence in cryptocurrency security. Their efficiency, dedication, and ethical approach made all the difference. I’m incredibly grateful to Vacuum Cyber Hack for their exceptional service and for proving that even in the most challenging situations, recovery is possible. They truly set the standard for Bitcoin recovery services. I can confidently recommend them as the best choice for anyone facing the same challenge.
Email: support @ vacuumcyberhack . com
Whatsapp: +39 351 059 0507
Website: https : //vacuumcyber hack .co m/2 -
Best in Recovery Stolen Bitcoin: Vacuum Cyber Hack can Help you out
When I realised my $395,000 worth of Bitcoin had been stolen, I was devastated. The thought of losing such a significant amount left me feeling completely powerless. After exhausting all options, I decided to reach out to Vacuum Cyber Hack. Their reputation for successfully recovering stolen cryptocurrency made them the obvious choice. From the very beginning, I was impressed by their professionalism and expertise. They quickly assessed my situation and immediately began working on a recovery plan. Using advanced algorithms and state-of-the-art forensic methods, Vacuum Cyber Hack tracked the stolen funds with remarkable precision. Throughout the process, they kept me updated, providing clear communication and ensuring my sensitive information remained confidential. Within a short time, Vacuum Cyber Hack successfully recovered my stolen Bitcoin, returning my funds and restoring my confidence in cryptocurrency security. Their efficiency, dedication, and ethical approach made all the difference. I’m incredibly grateful to Vacuum Cyber Hack for their exceptional service and for proving that even in the most challenging situations, recovery is possible. They truly set the standard for Bitcoin recovery services. I can confidently recommend them as the best choice for anyone facing the same challenge.
Email: support @ vacuumcyberhack . com
Whatsapp: +39 351 059 0507
Website: https : //vacuumcyber hack .co m/ 1
1 -
I've been working in sales for over a decade, building a successful business empire along the way. Wanting to expand my horizons, I decided to dive into the world of cryptocurrency, with a particular focus on Bitcoin. Using the wealth of knowledge available on the internet, I began my journey into this exciting and volatile market. Initially, my investment of $500,000 quickly grew, yielding a profit of over $700,000 in less than a year. Encouraged by this success, I deposited my earnings into a Bitcoin wallet. However, disaster struck when I lost my phone. After replacing it, I realized I could no longer access my wallet, triggering a frantic search for a solution. That's when a trusted trading colleague recommended CYBER TECH WIZARD. They promised to help me regain access to my account within 72 hours. With hope and skepticism, I reached out to them. From the very first interaction, the team at CYBER TECH WIZARD displayed remarkable professionalism. They patiently listened to my predicament and reassured me that they had the expertise to resolve it. Their clear and concise communication about the steps they would take helped put my mind at ease. They kept me informed throughout the process, providing regular updates on their progress. Their transparency and dedication were truly commendable. True to their word, within 72 hours, I received confirmation that my wallet access had been restored. Seeing my balance intact was an enormous relief. But CYBER TECH WIZARD didn't just stop at recovering my account. They went the extra mile to help me secure it against future mishaps. They guided me through implementing enhanced security measures, such as two-factor authentication and better backup protocols. Their proactive approach ensured that I was better protected moving forward. In summary, my experience with CYBER TECH WIZARD was outstanding. Their professionalism, expertise, and commitment to client satisfaction were evident at every step. They not only restored my access to my Bitcoin wallet but also helped safeguard my account against future issues. I highly recommend their services to anyone facing similar challenges in the cryptocurrency space. Thanks to their swift and effective intervention, I can now continue my trading journey with confidence, knowing my assets are secure
EXPERTISE INFORMATIONS
SEND EMAIL: cybertechwizard(@)cyberservices(.)com
WHATSAPP INFO:+185-9743-5022